
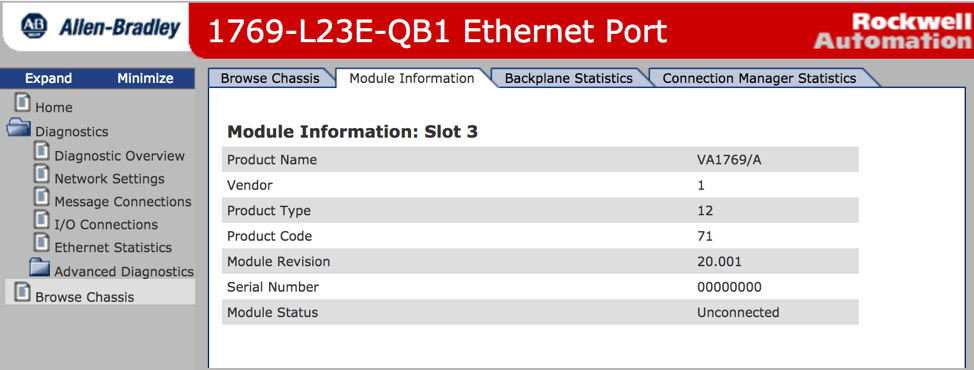
Tripwire Data Collector has been providing industrial organizations with visibility into their operational technology (OT) environments since its release in mid-2018. Data can be gathered and monitored via multiple avenues – not only native industrial protocols, such as EtherNet/IP CIP and Modbus TCP, but also integrations with management applications like Rockwell’s FactoryTalk AssetCentre, MDT AutoSave and Kepware KEPServerEX, as well as traditional IT protocols like SNMP and even HTTP. One difficulty observed in the field was problems gathering operational data protected behind a variety of web authentication methods. Tripwire Data Collector can monitor many different types of industrial devices, such as PLCs and RTUs, used in different sectors from energy and utilities to manufacturing. Many of these devices contain valuable information that may only be available via a web page.
Some of these web pages may be more protected than others with access available over SSL encryption or behind a custom authentication or security scheme. Not all devices use the common HTTP "basic authentication." Some may require complex authentication and then navigation across multiple pages in order to reach the prized asset data. We have to applaud device-makers for adding security features to operational technology devices, which have long lagged behind other aspects of information technology, but the wide variety of implementations necessitates creative auditing methods. Automated monitoring of your device status and configuration may feel like an insurmountable problem depending on the quantity and diversity of devices in your environment. Fortunately, Tripwire Data Collector provides a mechanism for monitoring such devices. One recent real-world scenario had us monitoring data from a device made by Schweitzer Engineering Laboratories. Interacting with this device in an automated fashion requires providing a username and password combination in the URL of an HTTP GET request and then scraping a session ID off the resulting webpage. That session ID must then be provided as a URL parameter in all subsequent requests. Tripwire Data Collector can be configured to log in to this type of device using a LUA scripting capability. Logging in and gathering a session id might be done in the following manner, where the configured username and password is sent in a GET request and the session ID is parsed from the resulting page:
body, stat, hdrs = request('/login.html?user='..auth.username..'&password='..auth.password)
match = string.match(body, "session_id=\x22([A-Fa-f0-9]+)\x22")
if table.getn(match) > 0 then
context["session_id"] = match[1]
end
Once established, any request can use the session id within a request like the following:
body, stat, hdrs = request('/page.html&session_id=’..context["session_id"])
This method of automated web information gathering is extremely powerful. Any information obtained from a device may be checked for configuration compliance or monitored for change all within Tripwire Enterprise. The Tripwire Industrial Control System (ICS) Security Suite is an ideal solution for many industrial organizations with complex OT devices. It enables visibility into device vulnerabilities and configurations that may have previously been unavailable to security teams. The Tripwire Data Collector natively supports Ethernet/IP CIP, Modbus TCP, SNMP and Web Retriever industrial protocols, and integrates with Rockwell FactoryTalk AssetCentre, MDT AutoSave and Kepware KEPServerEX. This combination allows for both light and no-touch approaches to reducing industrial cyber risk. Learn more about the Tripwire Data Collector and the Tripwire ICS Security Suite.
Request a Live Demo
Experience the power of Tripwire's cybersecurity solutions firsthand! Take a guided tour or participate in live demos to see how our products can enhance your organization's security. Start exploring now

