
Eight companies including Tripwire have been selected by the National Cybersecurity Center of Excellence (NCCoE) to collaborate on the Energy Sector Asset Management Project. The NCCoE is a part of the National Institute of Standards and Technology. These companies are working together to build a reference design and an example solution that can be used by energy companies to help identify, control and monitor their operational technology (OT) assets. The reference design and example solution are intended to demonstrate how cybersecurity best practices and standards along with today’s commercially available technologies, can produce an easily adaptable cybersecurity solution. In the last few years, a spotlight has been thrown on the security of energy networks by recent cyber-attacks. Profit-motivated hackers and politically minded state sponsored organizations have become increasingly active during the period. In 2015, three power distribution companies in Ukraine were simultaneously compromised in the first known attack on an electrical grid to generate a blackout. The “Crash Override” malware attack left 230,000 people without power for up to 6 hours. The sophisticated coordination of the attack suggested that a state actor was behind it. One year later, an advanced version of the malware was used to attack Kiev’s power grid. Twenty percent of Kiev’s power was blacked out in this incident. It is widely believed that Russia was using attacks on the Ukraine as a way of testing its cyber-warfare expertise. Additional attacks have occurred since then in Israel, Germany, France, Denmark, UK and the United States. Hackers looking for profit have repeatedly deployed ransomware, for example. At the same time, state actors including Iran and North Korea have penetrated into power companies and their control systems. In the most recent event in March 2018, the U.S. FBI and the DHS issued a warning stating that a, “multi-stage intrusion campaign by Russian government cyber actors” had targeted the networks of small commercial facilities “where they staged malware, conducted spear phishing, and gained remote access into energy sector networks.” NCCoE projects such as the Energy Sector Asset Management Project are designed to provide solutions to today’s pressing cybersecurity challenges. Each NCCoE project addresses unique cybersecurity challenges across energy, transportation, healthcare and other critical market segments. By providing example cybersecurity solutions that are specific to industry segments, the NCCoE is focused on accelerating adoption of cybersecurity and improving the security posture of U.S. businesses. The Energy Sector Asset Management Project focuses on securing OT energy assets by leveraging existing capabilities or implementing new capabilities. If you envision a power company as being split between the back office with its IT network and the “factory” portion of the company with its OT network, you have a rough understanding of the architecture. The image below highlights the focus area. The OT portion of the network includes devices that control generation and distribution of electricity as well as the communication networks that connect all of the component parts.
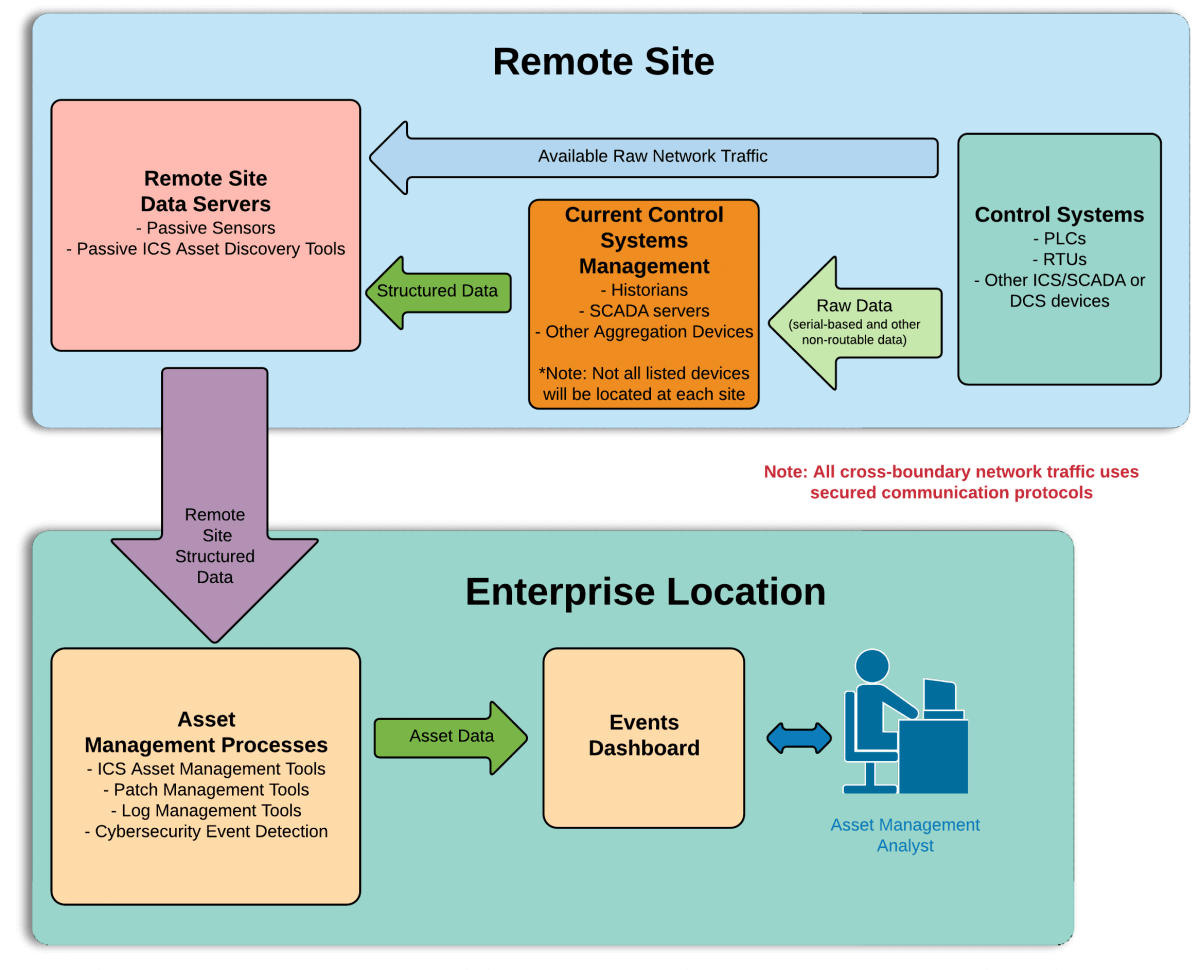
Credit: https://www.nccoe.nist.gov/ OT networks are different from IT networks in several significant ways. IT networks principally use Ethernet/IP and Modbus protocols. OT networks employ SCADA and SNMP communication and management technologies that talk to proprietary distributed control systems (DCS) and programmable logic controllers (PLCs). OT networks also place a priority on safety and “availability” or keeping the factory up and running. These issues are of a lower priority in IT networks. Tripwire brings a number of products to the table that address the unique problems associated with an OT network. For instance, OT systems are sensitive to identity and change monitoring probes. If done in the same manner as an IT system, the performance of the OT system can be significantly degraded. Tripwire has a number of products that are able to address the challenge of OT security.
Tripwire Enterprise
A security configuration manager that provides security monitoring, real-time change intelligence and threat detection. For the compliance officer, it delivers pro-active system hardening and automated compliance enforcement.
Data Collector
An add-on to Tripwire Enterprise that creates an agentless architecture (no software to install on endpoints). It also provides an innovative approach for industrial organizations to assess the configurations, security and status (including firmware, hardware revision, software versions, patch levels and more) in their environments. Tripwire Data Collector communicates via Modbus TCP, Ethernet/IP CIP and SNMP v1, v2, v3.
Tripwire IP360
A solution that proactively discovers, profiles and assesses the vulnerability risk of all wired and wireless devices. It prioritizes risk and provides remediation management through reporting and ticketing integrations.
Tripwire Log Center
A tool that provides secure and reliable log collection to add real-time intelligence with security analytics and forensics. Tripwire Log Center includes a growing library of available correlation rules. Tripwire appreciates the opportunity to work with the NCCoE and other contributing manufacturers to address the challenges of asset management in the energy sector. For additional information about defending industrial control systems, please download our whitepaper.
Achieving Resilience with NERC CIP
Explore the critical role of cybersecurity in protecting national Bulk Electric Systems. Tripwire's NERC CIP Solution Suite offers advanced tools for continuous monitoring and automation solutions, ensuring compliance with evolving standards and enhancing overall security resilience.

