Cybercrime is becoming more sophisticated by the day. Meanwhile, the price for a breach due to damage and disruption, ransom payments and regulatory fines, is increasing. No wonder there's more of a need than ever for companies to set up a dedicated SOC using SIEM to identify threats and raise the alarm. But is that enough to fight the hackers?
Understanding SOCs and SIEM Software
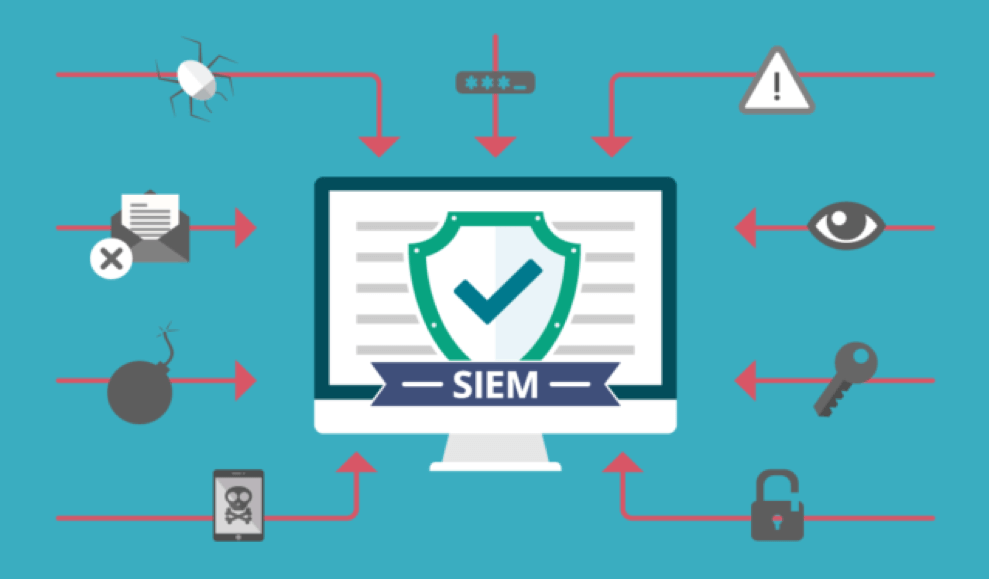
Although IT professionals will know all about SOCs and SIEM tools, business executives might need bringing up to speed. SOC stands for "Security Operations Center." Dealing with cyber security on a passive basis alone (e.g. through firewalls, intrusion detection systems (IDSs)) is like building a wall around a castle and just hoping the enemy doesn't find a way through or over it. Although there are different definitions, in most cases an SOC centralizes the security function of a business or organization. Setting up an SOC involves employing a team of people and setting up processes to monitor a host system or IT network and respond to any security incidents. Occasionally, one-person SOCs are found, but this is the exception. Every SOC needs some kind of SIEM tool. SIEM stands for Security Information and Event Management, and so SIEM software is a set of tools for providing the information needed to detect and manage security events. More specifically, SIEM tools aggregate and normalize data from various sources. This data can come from message logs (syslog), OS logs, end point devices, firewall/IDS output and network flow logs. Rather than simply logging all the data, SIEM tools then strip out anything irrelevant. This is called normalization. SIEM software then uses intelligent correlation rules to highlight links between events ready for analysis by a human IT support team. Analysts can then carry out NetFlow analysis and other techniques to investigate the reasons for any anomalies and, where necessary, take action to protect the business's IT infrastructure. Although every SOC will have some kind of SIEM software, this tool is also used by Cyber Incident Response Teams (CIRTs) and as part of other security-related IT services. LA, for example, has set up SIEM technology within its centralized cyber intrusion command center.
Going Beyond SIEM
While SIEM software is critical, is it sufficient?
One of the limitations of an SIEM tool is its focus purely on system-generated signals. When a cyber-attack is manually implemented, rather than carried out by malware, it can go unnoticed. Nevertheless, there may have been user-specific anomalies that could have indicated an impending threat. For example, a user in one department may have been logging into a system they rarely use on a number of occasions as they planned their moves. Or in another scenario, the login credentials of one employee may have been stolen in a phishing attack and used by an external attacker to try and access the system at an unusual time or simultaneously with the legitimate employee. These scenarios are the domain of user behavior analytics (UBA). By integrating UBA software with your SIEM tool, you now have a system capable of extending its pattern-matching capabilities from systems to users – both internal and external. Although setting up and running an SOC is, in itself, an active stance for a company to take, most are still quite reactive, spending a lot of time sifting through alerts. Even those that employ intrusion prevention technology may be slow to respond due to the size and complexity of the networks they are responsible for. Part of the problem is that most SIEM/UBA tools are still inadequate on their own. However, it is possible to integrate these with other specialized security tools. For example:
- Endpoint detection and response devices (EDR) for anything outside of the firewall
- Threat intelligence feeds
- Intruder traps (e.g. honeypots, honey files, honey users and honey credentials)
- Pre-built detections
- Central log management technology
Of course, companies need to make sure that they have the tech resource and know-how to integrate all of these tools into a sophisticated SOC. Another option is to go for a managed SOC service which can leverage the best security expertise and tools and also integrate with cloud-based SaaS applications. While this integration of SIEM, UBA and other security tools and processes will lead to fewer blind spots and more efficiency, there are other improvements waiting to be made. The vast majority of the data flagged by an SIEM tool is (thankfully) non-threatening. Nevertheless, analysts have to investigate each one in order to catch the 2-5% that, on average, correspond to real attacks. To cut down on the noise and improve efficiency, the infosec industry could take a leaf out of the medical sector. When paramedics arrive at the scene of a major accident, they don't put the same amount of effort into dealing with every incident they come across. This would be a disaster with trained personnel strapping up broken arms while more seriously injured victims are dying of blood loss! To avoid this, first responders use a triage system to quickly assess the severity of an individual casualty to enable them to prioritize treatment. A triage platform linked to an SIEM tool would enable analysts at a SOC to react fastest to the most obvious signs of attack instead of wasting resources wading through minor data discrepancies. Such a triage platform could also help analysts avoid alert fatigue whereby real attacks are missed due to the constant flow of false alarms. The SOC of the future, with integrated UBA and a triage platform, is now taking shape, but can we go even further? The faster an SOC can react to a cyber incident, the less likely there is of permanent and costly disruption to the business. Rather than wait for a member of the security team to act on the most urgent signals, orchestration software could be set up to automatically spring into action. For example, if the SIEM and UBA tools pick up signals that an attack is likely, while the triage platform is alerting the analysts to carry out urgent investigation, orchestration software could be already blocking IPs, removing user access and/or isolating networks as appropriate. Integrating case management features would also make it much easier for forensic teams to investigate the incident afterwards, storing and organizing system data and contextual information.
Imagining the SOC of the Future
As the IoT grows, the current SOC model is going to become increasingly obsolete. On the other hand, AI and machine learning is likely to make security software smarter. Although it is impossible to guess exactly what the SOC of the future will look like, by integrating SIEM, UBA and other tools with a triage platform, orchestration software and case management features, companies can at least begin the process of building a future-proof security center.

About the Author: Brent Whitfield is the CEO of DCG Technical Solutions Inc. located in Los Angeles, CA since 1993. DCG provides IT services for Los Angeles area businesses who need to remain competitive and productive, while being sensitive to limited IT budgets. Brent writes & blogs frequently and has been featured in Fast Company, CNBC, Network Computing, Reuters, and Yahoo Business. https://www.dcgla.com was recognized among the Top 10 Fastest Growing MSPs in North America by MSP Mentor. Because of Brent's experience as an MSP, he is actively serving on partner advisory councils for many of the major MSP vendors providing backup, RMM, and software to the market. He also leads SMBTN - Los Angeles, a MSP peer group that focuses on continuing education for MSP's and IT professionals. Twitter: @DCGCloud Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Tripwire Enterprise: Security Configuration Management (SCM) Software
Enhance your organization's cybersecurity with Tripwire Enterprise! Explore our advanced security and compliance management solution now to protect your valuable assets and data.

