
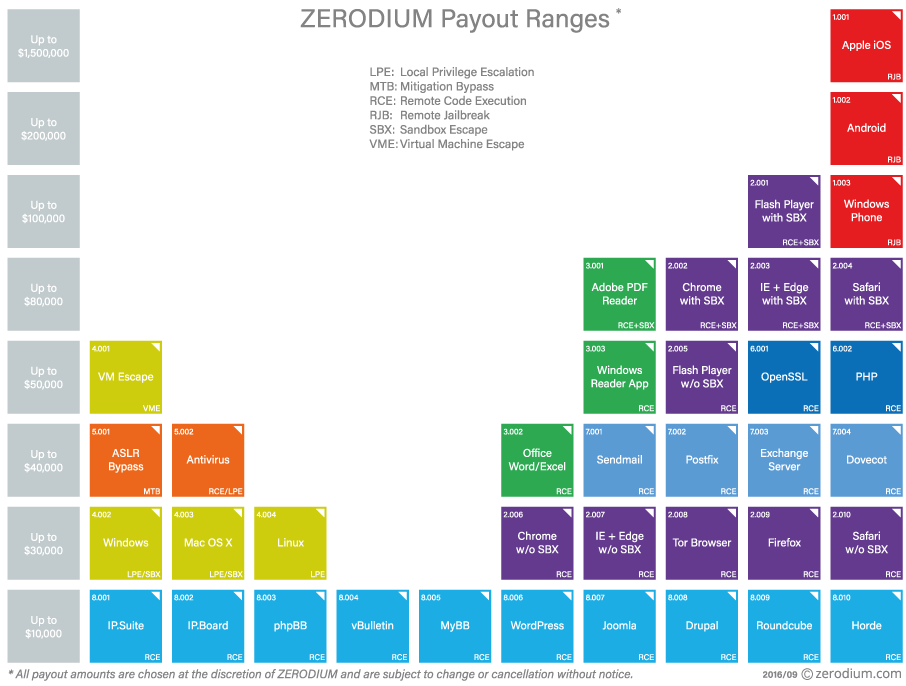
A company is offering to pay 1.5 million USD to anyone who submits a remote jailbreak for Apple's iOS 10. On Tuesday, the exploit broker Zerodium made the announcement on Twitter: https://twitter.com/Zerodium/status/781516292901789696 Zerodium is well known for offering bug bounty rewards whose value dwarfs those offered by Apple, Google, and other companies. For instance, the company made headlines back in September 2015 when it temporarily offered up to one million dollars (up from 500,000 USD) for iOS 9 vulnerabilities. That amount eclipses Apple's maximum payout of 200,000 USD for vulnerabilities that affect its firmware. (Not surprisingly, the Cupertino-based tech giant's recently announced bug bounty program does not cover iOS jailbreaks.) The vulnerability broker also generated some interest among hackers in January 2016 when it announced it would temporarily pay up to 100,000 USD for exploit code bypassing Adobe Flash Player's then-newly-added heap isolation defense. https://twitter.com/Zerodium/status/684308378949033985 Those rewards seem small compared to what Zerodium is now offering. In addition to announcing it will pay up to $1.5 million for a jailbreak of iOS 10, the company states it will now pay as much as 200,000 USD for a jailbreak of Android Nougat (up from 100,000 USD) and 100,000 USD for a remote code execution flaw in Adobe Flash with sandbox escape (up from 80,000 USD).
Okay...so why such high rewards? Well, on the one hand, Zerodium requires a lot of those who decide to submit an entry to its program. For example, with its iOS 9 campaign, the broker required that participants turn in one of three things:
- a web page targeting the mobile browser (Mobile Safari OR Google Chrome) in its default configuration; OR
- a web page targeting any application reachable through the browser; OR
- a text message and/or a multimedia file delivered through a SMS or MMS.
On the other hand, Zerodium is not interested in security. It sells all vulnerabilities it collects in undisclosed form to its clients, which founder Chaouki Bekrar told WIRED Magazine consists of governments and corporations in North America as well as government agencies in "allied countries." If responsible disclosure is your game (like it is ours), this isn't the way to go. To learn more about Zerodium and how its vulnerability payout system works, please click here.

