
Threat actors victimized more than 1.5 million computer users with cryptocurrency mining software in the first eight months of 2017. It's perfect legal for users to install software on their computers that mines cryptocurrency. But miners are unique in that many of them come with the ability to achieve persistence on a system, to automatically launch on boot-up, and to conceal their operations. Threat actors are familiar with these features, which is why they attempt to install such software on users' computers without their knowledge. Most of the time, attackers leverage social engineering and conceal otherwise legitimate miners inside of free adware installers. They can either try to enlist the help of a less-than-ethical adware provider or build droppers for cryptocurrency miners by clicking on advertisements posted on Telegram channels. These customizable tools come with the ability to suspend the software if the user launches a popular game like Black Ops 3, GTA V, and World of Tanks.
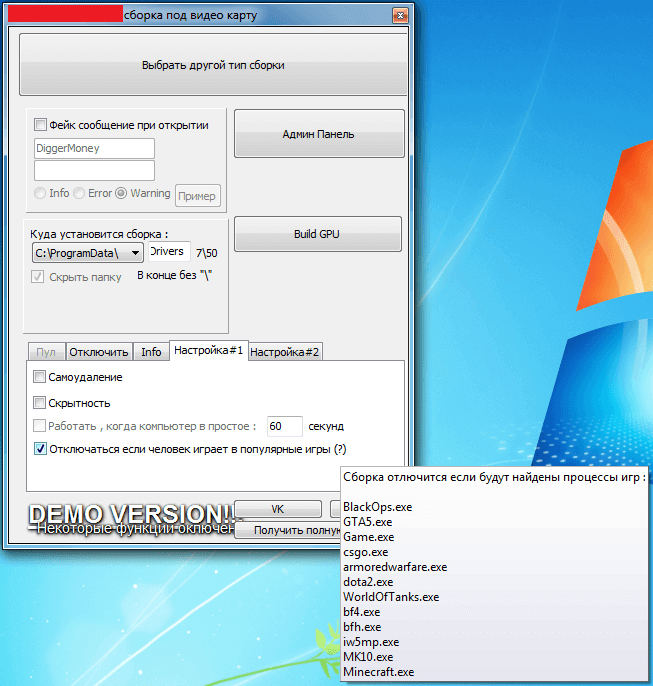
The demo of a miner's builder advertised on Telegram. (Source: Securelist) But adware installers aren't the only propagation method for cryptocurrency miners. In some cases, threat actors leverage vulnerabilities like EternalBlue to sow software onto unsuspecting users' computers. In others, they conceal the miners inside installers for pirated copies of popular games. Attackers can use successfully installed miners to secretly mine for relatively new cryptocurrency like Monero (XMR) and zcash. This process will slow down the victim's computing experience because miners traditionally require lots of processing power. That's especially true if the attackers manage to victimize a server operated by a large organization. That's not all. Nefarious individuals can potentially leverage this software to turn off security software and track all application launches. Unfortunately, the threat of bad actors surreptitiously installing cryptocurrency on unsuspecting users' computers is on the rise. As Kaspersky Lab's Evgeny Lopatin and Vladas Bulavas explain:
"In general, the number of users that have encountered cryptocurrency miners has increased dramatically in recent years. For example, in 2013 our products protected around 205,000 of users globally when they were targeted by this type of threat. In 2014 the number increased to 701,000, and the number of attacked users in the first eight months of 2017 reached 1.65 million."
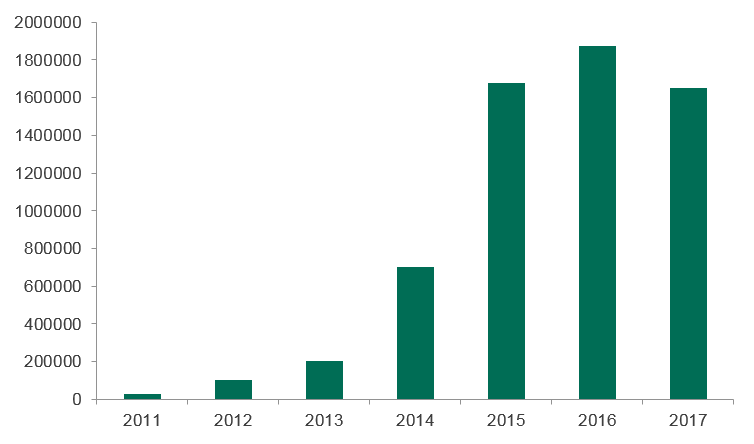
Number of users Kaspersky Lab protected from malicious cryptocurrency miners from 2011 to 2017. (Source: Securelist) Users and businesses should therefore work to protect themselves against cryptocurrency mining threats. They can do so by exercising caution around or completely avoiding freeware installers as well as not clicking on suspicious links and email attachments. They should also make sure they stay on top of the latest software updates. To learn how Tripwire's products can help streamline your company's patch management processes, click here.

