
A single Monero cryptocurrency mining operation has used malware delivery techniques to affect at least 15 million people worldwide. The campaign, which has been active since at least October 2017, delivers its payload using one of 250 unique Microsoft Preinstallation Environment (PE) files like "File4org]_421064.exe" and "[Dropmefiles]_420549.exe." The files appear to come from popular file-sharing services. They all ultimately download a piece of malware detected by Malwarebytes as "trojan.bitcoinMiner." This campaign's malicious payload uses NiceHash, a hashing processing power marketplace which temporarily ceased operations in December 2017 following a security breach. The trojan also uses a cryptominer known as XMRig to mine for Monero. All at the expense of an infected computer's CPU. Those behind this operation have updated the malware's behavior at least four times. Up until 20 October 2017, the payload dropped a VBS file (and LNK file for persistence). The VBS file, in turn, used the BITSAdmin tool to download scrips and XMRig from a remote location.
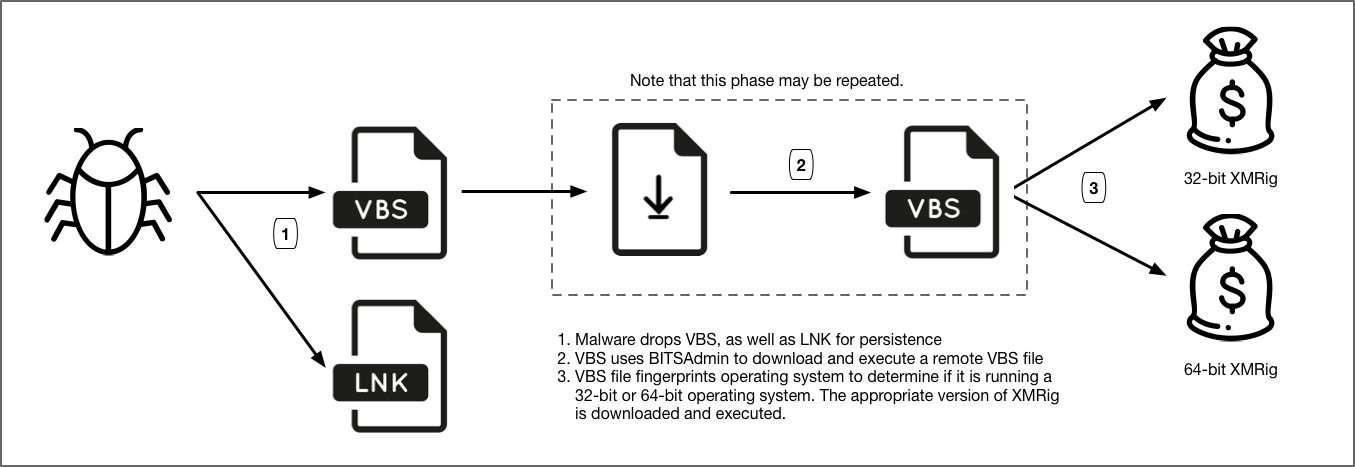
Execution workflow for the oldest malware encountered in this campaign. (Source: Palo Alto Networks) Things changed after 20 October 2017 when the initial VBS file dispensed with BITSAdmin and began using HTTP redirection services like bit.ly. Through this link shortener in particular, Josh Grunzweig has come up with an estimate of how many people this campaign has likely affected:
Based on publicly available telemetry data via bitly, we are able to estimate that the number of victims affected by this operation is roughly around 15 million people worldwide. This same telemetry provides insights into the most heavily targeted areas involving this campaign, which impacts southeast Asia, northern Africa, and South America the most. However, it’s important to note that the actual number of victims is likely much higher because less than half of the samples we identified in this campaign leverage bitly. If we postulate that the bitly telemetry is typical for this operation, we can extrapolate to speculate that as many as 30 million people have been affected by this operation. While the actual number could be more or less, this does serve to give an idea of the possible size and scope of this large scale operation.
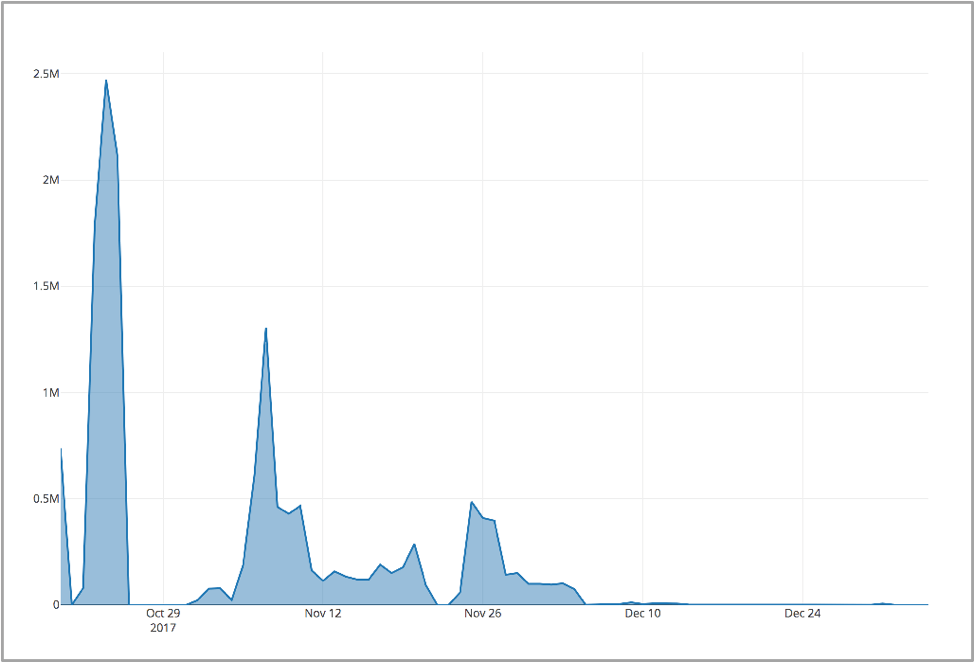
Malicious bitly downloads over time. (Source: Palo Alto Networks) The countries most commonly hit by this campaign include Thailand, Vietnam, Egypt, and Indonesia. Two other changes occurred in November and December 2017 that altered the delivery mechanism for the initial VBS file. Overall, this campaign didn't do anything that other campaigns haven't done before. Yet Christopher Budd of Palto Alto Networks feels it still spells trouble for the future:
... [G]iven how quickly and broadly successful it is, combined with the continued high value of cryptocurrencies, we can also conclude that attackers will continue to focus on cryptocurrency and likely will evolve their techniques and tactics quickly. Cryptocurrency-focused threats is a key area that all defenders should focus their intelligence and prevention efforts around in 2018.
Let's hope security professionals do just that. Palo Alto Networks is a member of Tripwire's Technology Alliance Program (TAP). To learn more about TAP, click here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

