
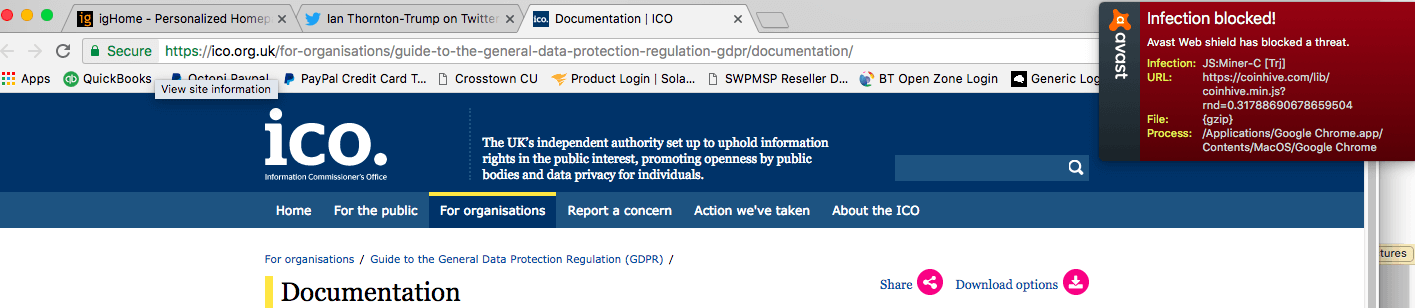
Bad actors secretly infected more than 4,000 websites with the script for a crypto-miner after hacking a single technology provider. The trouble started on 11 February when Ian Thornton-Trump encountered something concerning while visiting the website for the UK Information Commissioner's Office (ICO). https://twitter.com/phat_hobbit/status/962683226471923713 The LinkedIn-shortened URL leads to a post containing a screenshot of the researcher's visit to the ICO website. Clearly visible at the top right-hand corner of the page is a security warning indicating the presence of a crypto-miner:
Source: Ian Thornton-Trump Thornton-Trump didn't believe what he was seeing at first. As he told The State of Security in a DM:
You need to know when you're out of your depth. I knew a highly trusted page should not be throwing AV errors, so at first I thought it was me. I’ve seen Scott Helme present at numerous conferences, so I reached out to him. He confirmed I was seeing a malicious JavaScript that was attempting to load a cryptominer on the ICO’s website.
https://twitter.com/Scott_Helme/status/962684239975272450 Helme, an information security consultant, got to work exploring what had caused ICO's website to load up a crypto-miner. He quickly discovered that the offending script for CoinHive, a popular crypto-miner which Check Point named the "most wanted" malware in December 2017, was not hosted by the ICO. Instead he traced the script back to Texthelp, a provider of software which makes websites more accessible for people with dyslexia and other reading difficulties. Here's what the security consultant found out about the infection:
If you want to load a crypto miner on 1,000+ websites you don't attack 1,000+ websites, you attack the 1 website that they all load content from. In this case it turned out that Text Help, an assistive technology provider, had been compromised and one of their hosted script files changed. The offending asset can be found here (https://www.browsealoud.com/plus/scripts/ba.js) for the duration it remains but here is the snippet that matters.
Indeed, more than 4,000 websites contained the CoinHive script following the Texthelp hack. Those include City University of New York, the UK Student Loans Company, and others. After learning of the hack from Helme, Texthelp disabled its Browsealoud feature. Martin McKay, CTO and data security officer, also released a statement acknowledging the attack and reassuring customers that the incident had not affected their data. Thornton-Trump feels that all domain owners can learn something from this episode:
The aftermath of this type of supply chain cyber security problem is ever present. We have talked on how to prevent the attack; there is debate on whether Content Security Policy and/or Sub resource integrity checking would have stopped or prevented the malicious script from running. What is clear is that cyber criminals are moving hard and fast with their attack techniques and improving their abilities. Crypto-mining opens up endless possibilities of revenue if systems are insecure or even better if they are left to languish. If you're a trusted site on the internet today, all the components of your site need to be secure. If one fails, you fail. It’s your website, so it needs to be looked after and secured if you want to keep the trust of the customer.
To learn more about how to prevent this type of attack, check out Helme's posting. Click here to learn how Tripwire can help your organization defend its website and other IT assets using foundation security controls.

