
Wannabe computer criminals can now easily create Android ransomware thanks to what are known as trojan development kits (TDKs). TDKs automate the process of developing new mobile malware by leveraging a version of the computer-aided software engineering (CASE) tool model. These device-aided malware engineering (DAME) utilities enable an actor to quickly create a ransomware variant on their devices. All they need to do is install an application containing a TDK. Unfortunately, such programs aren't hard to find. Symantec Security Response detected one such app advertised on hacking forums and a popular Chinese social media platform. It leads a wannabe malware developer through the process of specifying the new ransomware's display message on a victim's locked screen, the key needed to unlock the device, an icon displayed by the malware, algorithms used to randomize the program's code, and animation that will display on the infected device. With an easy-to-use interface, computer criminals with low levels of technical expertise would have no problem filling out the on-screen customization form.
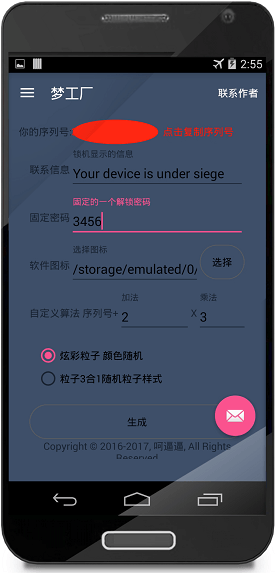
The malware generator app. (Source: Security Response) Dinesh Venkatesan of Security Response explains what happens after a user finishes setting the ransomware's parameters:
"... [T]he user hits the “create” button and, if they haven’t already done so, is asked to subscribe to the service. The app allows the user to start an online chat with the app’s developer where they can arrange a one-time payment. Once the user has subscribed, they can continue with the process, making as many ransomware variants as they desire."
All that remains then is for the user to decide how they'd like to distribute their ransomware to unsuspecting users. For those who fall victim to the attack campaign, the malware locks their device and demands a ransom payment in exchange for the unlock key.
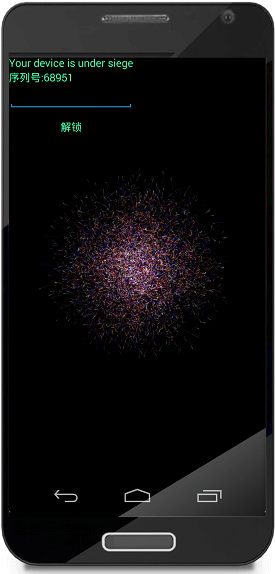
The ransomware created using the Trojan Development Kit in action. (Source: Security Response) At this time, it appears the app discovered by Venkatesan and his colleagues targets Chinese users mainly. The TDK also creates only lockers and not encrypters. But none of that is set in stone. The app's creators could modify their program with expanded language support and built-in encryption capabilities. Not to mention how other malicious app developers might be spending their time. Given these threats, it's imperative that mobile users follow some simple steps to prevent a ransomware infection. They should, for instance, update their devices on a regular basis and install a mobile anti-virus solution onto their phones. They should also back up their mobile data on a regular basis. For additional ransomware prevention strategies, click here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

