
A new Android trojan targets wireless routers and performs DNS hijacking instead of attacking users directly. Kaspersky Lab found that the trojan, dubbed Trojan.AndroidOS.Switcher, generally adopts one of two disguises. The first facade (com.baidu.com) is a fake mobile client for the Chinese search engine Baidu. The second (com.snda.wifi) is a fake version of another app that allows users to share information about public Wi-Fi networks.
The two fake apps. (Source: Kaspersky Lab) Once a user downloads one of the two camouflaged applications, Switcher gets to work. It first obtains the BSSID, or the MAC address of the wireless access point (WAP), and informs its command and control (C&C) server. It then tries to identify the ISP to determine which of its three rogue DNS servers it should use: 101.200.147.153, 112.33.13.11, and 120.76.249.59. Next, the trojan performs a brute-force attack using a number of predefined usernames and passwords. As of this writing, its attack code works against only TP-LINK Wi-Fi routers. Kaspersky mobile malware analyst Nikita Buchka explains in a blog post what happens if Switcher enters the correct login credentials:
"If the attempt to get access to the admin interface is successful, the trojan navigates to the WAN settings and exchanges the primary DNS server for a rogue DNS controlled by the cybercriminals, and a secondary DNS with 8.8.8.8 (the Google DNS, to ensure ongoing stability if the rogue DNS goes down)."
Attackers can use those two rogue DNS servers to steer anyone who accesses the web through the compromised router away from their desired destination. If a user searches for Google.com, for example, the bad actors can redirect them to a site that's laden with malware under their control. Alternatively, they can save all of a user's search results and web traffic.
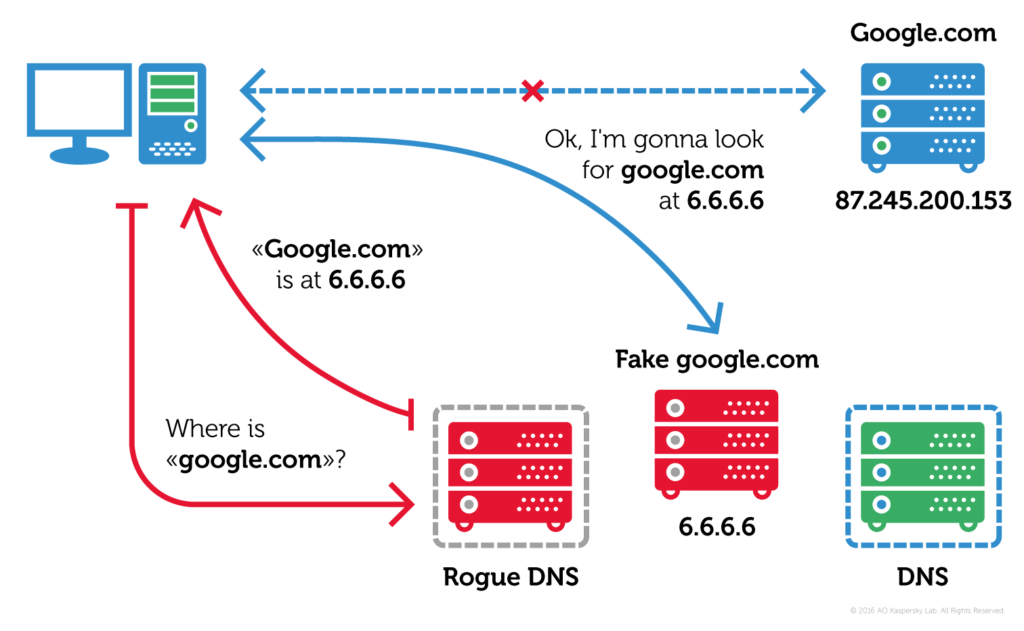
An explanation of DNS hijacking. (Source: Kaspersky Lab Switcher has compromised more than 1,000 wireless networks thus far. But it's unlikely to stop there. And given the ever-growing number of Android malware (and ransomware), there will no doubt be other Android trojans that perform DNS hijacking in the future. With that in mind, users should protect themselves by downloading applications only from legitimate app stores such as Google's Play Store and Apple's App Store. They should also change their router's default login credentials so that Switcher, Mirai, and similar malware samples can't compromise it using a brute-force attack.
Zero Trust and the Seven Tenets
Understand the principles of Zero Trust in cybersecurity with Tripwire's detailed guide. Ideal for both newcomers and seasoned professionals, this resource provides a practical pathway to implementing Zero Trust, enhancing your organization's security posture in the ever-evolving digital landscape.

