
Apple has released an update that is designed to better protect passwords for encrypted APFS volumes on machines running macOS High Sierra. APFS is short for Apple File System. The Cupertino-based tech giant created it to fix some issues involving Mac OS Extended. Apple File System is meant for computers with flash or solid-state drive (SSD) storage with a focus on encryption. For computers with macOS High Sierra (10.13) installed and all-flash storage, APFS serves as the default file system. Shortly following High Sierra's public release on 25 September, developer Matheus Mariano spotted a vulnerability involving the new operating system and APFS. He created an encrypted APFS container, set a password ("mypassword") with a hint, unmounted the container, and mounted it again. While unlocking his container, he decided to show the password hint to make sure his clue displayed correctly. Instead, the hint revealed the developer's password.
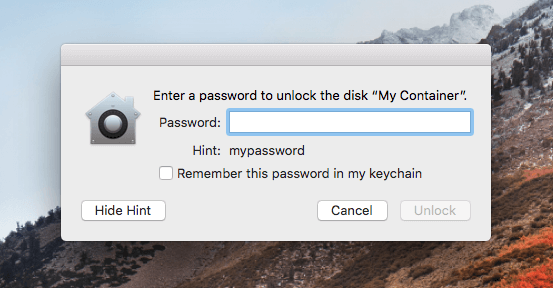
A screenshot of the APFS log-in window showing Mariano's password in the password hint. (Source: Matheus Mariano on Medium) Mariano was surprised by the issue, which according to MacRumors appears to affect only the Disk Utility of machines with SSD storage and not the process of creating an encrypted APFS volume in Terminal with the diskutil command line utility. As he writes on Medium:
"I really don’t know how this went unnoticed by Apple (and anyone else). Anyway, it was already reported to Apple by me."
It's unclear if Apple responded to Mariano. Since receiving the developer's report, however, the tech company has released a supplemental update for machines already running High Sierra with SSD storage. The fix not only addresses the issue spotted by Mariano but also addresses an issue previously identified by Patrick Wardle of Synack whereby an attacker could extract passwords from the Keychain. https://twitter.com/patrickwardle/status/912254053849079808?lang=en Apple has also released a support document explaining how users can best protect their encrypted APFS volumes after they've installed the supplemental update. It's recommended that affected users implement the fix and follow the tech giant's guidance as soon as possible. News of this issue comes more than a year after Apple patched three zero-day vulnerabilities that could allow an attacker to silently jailbreak an iOS device and spy on victims.

