
Two Belgian security researchers have developed a method that allows an attacker to exploit weaknesses found in the RC4 encryption algorithm and subsequently expose information that was once thought to be encrypted. According to a blog post written by Mathy Vanhoef and and Frank Piessens of the University of Leuven, their RC4 NOMORE attack concentrates on decrypting web cookies, which are generally protected by the HTTPS protocol.
"Websites use these cookies to identify users and authorize actions they perform," the researchers explain. "By obtaining the cookie of a victim, an attacker can log into a website as if he were the victim."
Using a separate non-HTTPS-protected website, the researchers developed a proof-of-concept attack against a fictitious website and victim in which they injected malicious Javascript code into their target HTTPS-protected site. This code caused the victim to transmit encryption requests which contained the victim's cookie in rapid succession. Previous attacks required 13 * 230 encryptions of a cookie to be able to decrypt it, and they limited the number of victim encryption requests to 1700 per second. Together, these two conditions meant that it generally took approximately 2000 hours to deduce a cookie's contents. This new method of attack, however, allows the victim to send 4500 requests per second and requires only 9 * 227 encryptions of a cookie. After 75 hours, and in as little time as 52 hours, the researchers were able to accurately guess the contents of a user's cookie 94% of the time.
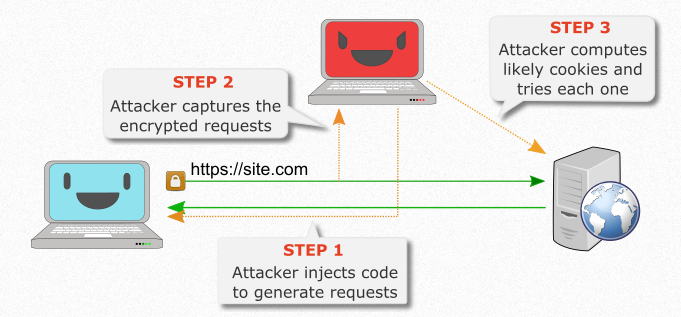
Source: RC4 NOMORE Vanhoef and Piessens demonstrate their attack in a video shown here. As for WPA-TKIP, the researchers used a method that allowed them to generate a large number of identical packets. By generating the plaintext candidate list and using a redundant packet structure to weed out unlikely choices, they were able to decrypt the packet, obtain the TKIP MIC key, and subsequently inject and decrypt packets. This method of attack took only an hour to execute.
"We consider it surprising this is possible using only known biases, and expect these types of attacks to further improve in the future," the researchers wrote in a paper. "Based on these results, we strongly urge people to stop using RC4."
Vanhoef and Piessens will present the RC4 NOMORE attack and their research findings at this year's USENIX Security Symposium, one of The State of Security's five gems in the world of information security conferences.

