
The developers of Cerber ransomware have equipped their creation with the ability to steal victims' Bitcoin wallet files. Security researchers first discovered Cerber in early 2016. Since then, the crypto-malware family has gone through at least six iterations. It's also sparked a ransomware-as-a-service (RaaS) platform that's raked in upwards of a million dollars a year in ransom payments for its authors. The ransomware has kept certain elements constant across its fast-paced evolution. Cerber still arrives via malspam with an attached file, for instance, and it still prefers Nemucod malware as its downloader.
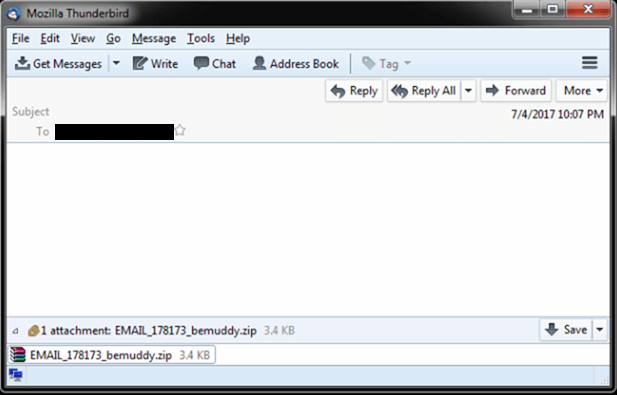
Cerber arrival. (Source: Trend Micro) But ransomware developers are not change-averse. They're always looking for ways to monetize their malware. That explains why the creators of Cerber have equipped their enciphering strain with the ability to steal victims' Bitcoin wallet files. Trend Micro's Gilbert Sison and Janus Agcaoili elaborate on this new behavior:
"How it goes about this is relatively simple: it targets the wallet files of three Bitcoin wallet applications (the first-party Bitcoin Core wallet, and the third-party wallets Electrum and Multibit). It does this by stealing the following files, which are associated with their respective applications: wallet.dat (Bitcoin), *.wallet (Multibit), [and] electrum.dat (Electrum)."
The baddy also targets saved passwords from Internet Explorer, Google Chrome, and Mozilla Firefox all before initiating its encryption routine. Credential theft is key to Cerber's newest monetization scheme. The ransomware steals (and then subsequently deletes) a user's Bitcoin wallet files only. To make off with their Bitcoins, it requires the password that protects the stolen files. Users can protect themselves against this updated ransomware variant by exercising caution around suspicious links and email attachments. Next, they should refrain from storing their passwords in a web browser and instead use a password manager to save their login credentials. Lastly, they should back up their data on a regular basis just in case they suffer a ransomware infection.

