
A new ransomware called "CryptoLuck" is infecting victims via a legitimate, code-signed program from Google known as "GoogleUpdate.exe." Security researcher Kafeine spotted the RIG-E (Empire) exploit kit distributing CryptoLuck via malvertising. It's not the first time they've detected an exploit kit campaign distributing ransomware. In this particular case, all of the malicious activity has thus far originated from adult websites, though it's possible attackers could also be abusing compromised sites to redirect users to RIG-E. CryptoLuck lands on a user's computer with a RAR SFX file that includes crp.cfg, GoogleUpdate.exe, and goopdata.dll files. The SFX file also contains a series of instructions, including the silent execution of GoogleUpdate.exe once all of those files are extracted to the %AppData%\76ff folder. On its own, GoogleUpdate.exe isn't so bad. It's a legitimate, code-signed software component of Google Updater. Essentially, it's responsible for running Updater, a program which is responsible for installing, removing, and updating Google applications.
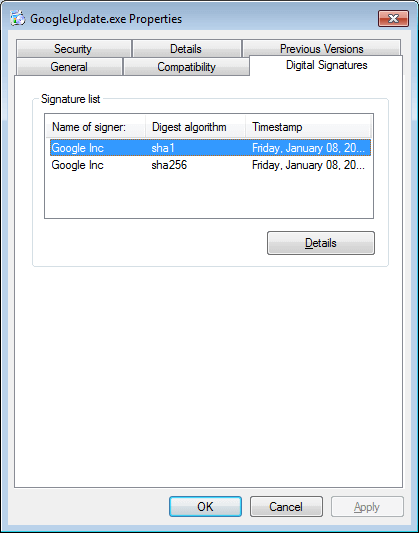
Signed Google Executable (Source: Bleeping Computer) But GoogleUpdate.exe isn't so nice when it's paired with a malicious goopdate.dll file. Lawrence Abrams of Bleeping Computer explains:
"When the GoogleUpdate.exe program is run, it will look for a DLL file called goopdate.dll file and load it. The problem is that it will first look for this file in the same folder that the GoogleUpdate.exe resides in. This allows a malware developer to create their own malicious goopdate.dll file and have it loaded by GoogleUpdate. "This is the case with the CryptoLuck developer, who had put all of the ransomware related code into their own malicious goopdate.dll file. Then when the legitimate GoogleUpdate.exe file is executed it loads the malicious DLL rather than the legitimate one normally used by Google."
After checking to see if it's running on a virtual machine, CryptoLuck scans for certain file extensions on the computer, mounted drives, and unmapped network shares. The ransomware bears two gifts for each targeted file it finds: a unique AES encryption key that it uses to encrypt the file and a .[victim_id]_luck appended file extension. Once its encryption process is complete, all CryptoLuck needs to do is announce itself to its newest victim.
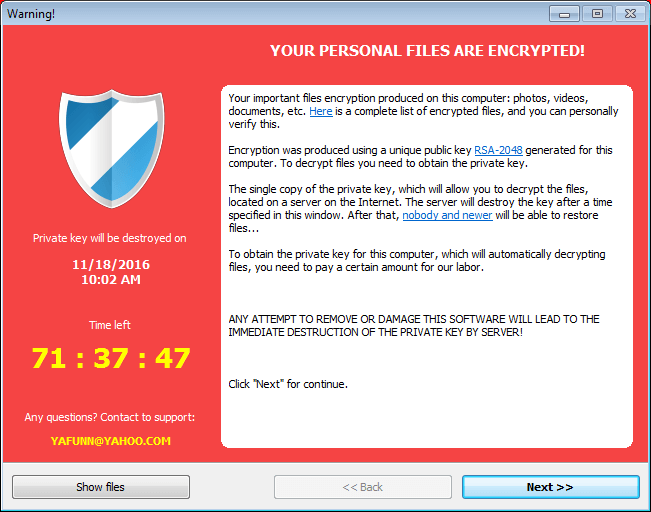
CryptoLuck (Source: Bleeping Computer) The ransomware developer demands that victims pay a fee of 2.1 Bitcoins (approximately 1,500 USD) within 72 hours if they want to regain access to their files. As each file is encrypted with its own AES key, and as only the developer has the master key, CryptoLuck can't be decrypted for free. That's why users need to make sure they implement a data backup strategy now just in case they run into the ransomware later. The last thing you ever want to do is pay the ransom and help legitimize what these criminals are doing to innocent people. Click here for more anti-ransomware prevention strategies. You can also learn more about ransomware in general here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

