
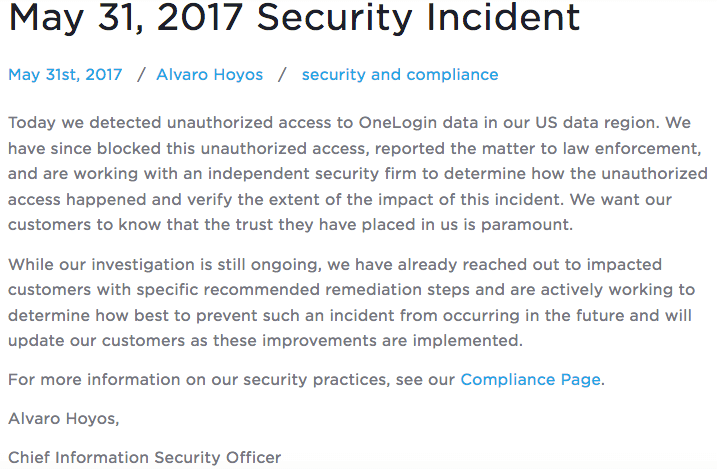
Identity and access management software vendor OneLogin has suffered a security incident that reportedly compromised customer data. On 31 May, the provider of identity-driven security solutions revealed that an unauthorized party had gained access to OneLogin data in the U.S. region. Alvaro Hoyos, chief information security officer at OneLogin, explains the company is in the process of responding to the incident:
"While our investigation is still ongoing, we have already reached out to impacted customers with specific recommended remediation steps and are actively working to determine how best to prevent such an incident from occurring in the future and will update our customers as these improvements are implemented.
Hoyos provides scant information about what actually happened in his blog post. He mentions only "unauthorized access". Nothing more. But emails sent to customers and obtained by The Register paint a clearer picture. The security notices link to a customers-only support page, which further describes what happened. As quoted by The Register:
"All customers served by our US data center are affected; customer data was compromised, including the ability to decrypt encrypted data."
It then provides a list of actions that affected customers should take as soon as possible. These pressing responses include forcing a OneLogin directory password for users, generating new API credentials and OAuth tokens, and creating and applying new desktop single sign-on (SSO) tokens. A OneLogin customer described the incident to Motherboard this way:
"Dealing with aftermath. This is a massive leak."
This isn't the first time a security incident has exposed web users' passwords, API keys, and OAuth tokens. In the spring of 2014, URL shortening service Bitly suffered a breach that exposed those three pieces of data along with users’ email addresses. As part of its notification process, Bitly provided customers with instructions on how they could reset API keys and OAuth tokens. OneLogin confirmed it blocked the "unauthorized access" responsible for the incident. It also said it's working with law enforcement to better understand what happened.

