
A research team is blaming dark web sellers and websites for foolishly uploading geotagged images to underground marketplaces. Paul Lisker and Michael Rose, who are both Harvard students of CS and Government , authored a study in which they asked the following question: is it possible dark web users are unwittingly revealing their location as they post images to undergrounds markets? For their research, they used the freely available Black-Market Archives to collect and analyze images from dark net markets (DNMs) that contain EXIF data. That information can include, for example, details about which camera make and model took a photograph and even GPS location coordinates, as is commonplace with images taken by smartphones.

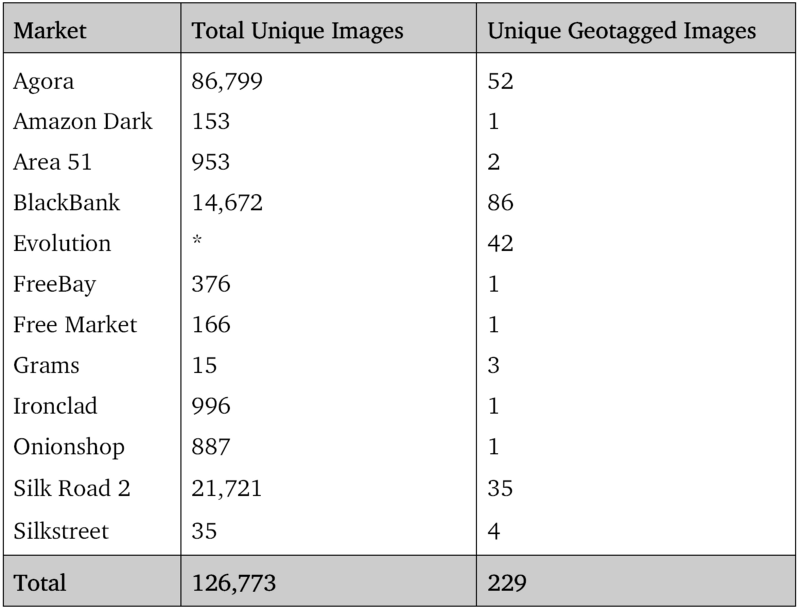
A collage of various pictures of illicit and regulated goods found in the black-market archives Using Python and Bash scripts, the duo checked for EXIF data and saved any location coordinates to a text file. They then used that information to determine how many unique geotagged images they came across. In total, the researchers found 7,522,284 images. 223,471 of those photographs were unique, though only 229 contained EXIF information.
Lisker and Rose came across some interesting discoveries over the course of their analysis, especially with regards to the Agora marketplace. As they explain in a blog post:
"Agora presents an interesting case: from the archive’s beginning on January 1, 2014 through March 18 of that year, we identified 963 non-unique tagged images — the most of any market in the study. However, after March 18 we found zero images with location data through the end of the archive. The sudden cut off from what was previously a plentiful source of images suggests that the site’s administrators may have discovered this geotag vulnerability and instituted some form of metadata removal after this date."
Overall, the researchers blame dark web sellers for their own stupidity in uploading images without removing their EXIF information first. They also think underground marketplaces are responsible for a "significant security oversight" in not following Facebook's lead and simply refusing to display images' EXIF location.
Lack of concern over users' anonymity has unraveled many underground markets in the past. In 2015, for instance, authorities arrested several individuals who administered Playpen, an underground child pornography website which failed to properly set up a Tor-based server. That takedown continues to influence law enforcement's relationship to the digital world even today.
Going forward, the duo thinks other research teams could study the viability of creating a tool that identifies geotags in dark web listings.

