
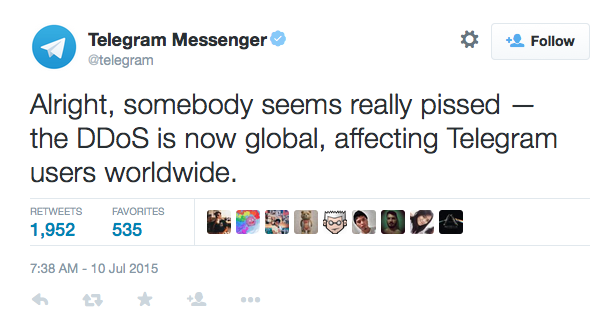
A DDoS attack continues to affect the Asian Pacific servers of messenger app Telegram as of Monday morning. The attack was first revealed by the company on Twitter early Friday morning. Four hours after its initial announcement, Telegram posted again, stating that the attack had become global and was now affecting users' access worldwide.
Source: Twitter Connectivity for the app, which has attracted a number of South East Asian users away from popular messaging services such as WhatsApp and WeChat, was spotty over the weekend. The company has since released a statement explaining that the attack is still ongoing.
"Just in case you're not following us on Twitter, Telegram's Asia Pacific server cluster has been under a DDoS attack since Friday morning," the statement reads. "This means that if you live in South East Asia, Oceania, Australia or certain parts of India, you may have been experiencing slower connection speeds or no connection at all for several hours this past weekend."
Telegram goes on to explain that it has been hit by 200 Gbps of junk traffic. The attack appears to be a Tsunami SYN Flood, a new type of DDoS attack in which malicious actors transmit very large SYN packet sizes, sometimes as many as 1,000 bytes, which complicate most anti-DDoS defense algorithms. Even so, the attackers behind the Telegram DDoS campaign appear to be flexible with their tactics. Most of the garbage traffic has originated from approximately one hundreds thousand infected servers, including LeaseWeb B.V., Hetzner Online AG, PlusServer AG, NFOrce Entertainment BV, Amazon and Comcast networks. According to a thread posted on Hacker News, the company currently suspects that actors based in South Korea are responsible for the attack. This suspicion is supported by two previous DDoS attacks originating from that region against Telegram, one back in September of 2014 and another one in June of this year. The company most recently reported that it has remained online for 95% of its users. As for the other 5%, it reports that its "sysadmin cyborgs are working on this 24 hours a day." News of this attack follows a report released by Akami earlier this year revealing that DDoS attacks grew by 90 percent in Q4 of 2014. This is no doubt due to the work of DD4BC and other threat actors.

