
Researchers have created a decryption tool for MIRCOP ransomware that demands 30,000 USD in ransom from its victims. Trend Micro explains the ransomware is currently being delivered via malicious macros as part of a spam campaign. Users open what appears to be a Thai customs document for importing and exporting goods. But when they click to enable macros, they download and execute MIRCOP. The ransomware drops three files onto a user's computer. One of those files encrypts all of a user's files using Data Encryption Standard (DES) encryption and prepends the filename ".Lock" onto each encrypted file.
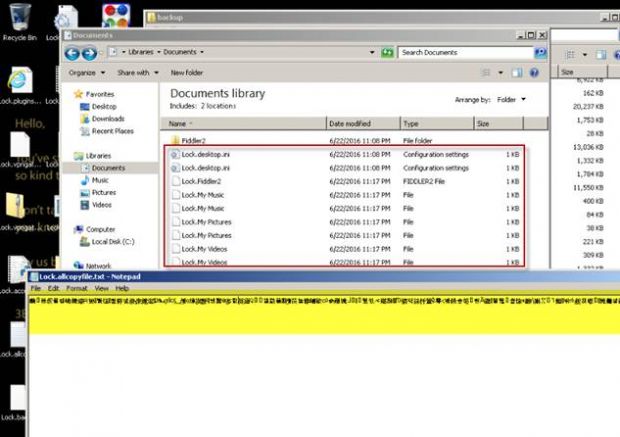
Files encrypted by MIRCOP (Source: Trend Micro) MIRCOP then displays its ransom message, which is accompanied by the image of a hooded figure wearing a Guy Fawkes mask:
"Hello, // You've stolen 48.48 BTC from the wrong people, please be so kind to return them and we will return your files. // Don't us for fools, we known more about you than you know about yourself. // Pay us back and we won't take further action, don't pay us and be prepared."
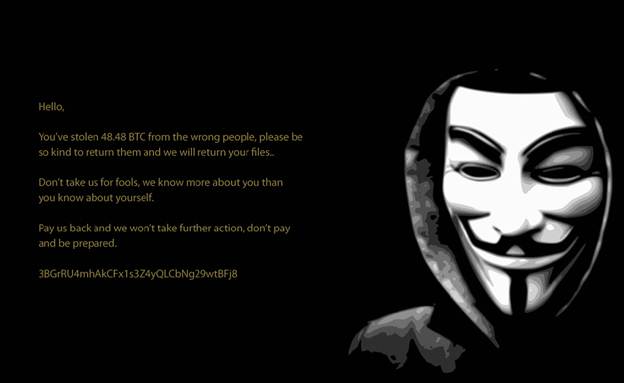
MIRCOP's ransom note (Source: Trend Micro) Unlike other crypto-ransomware, MIRCOP doesn't provide users with any instructions on how to make a payment using Bitcoin. It also demands 48.48 BTC (32,956.70 USD as of July 3, 2016) from its victims--by far one of the largest ransom demands security researchers have ever seen from a single ransomware infection. No transactions have been logged with the malware's Bitcoin address as of this writing, which means victims of the ransomware have yet to give in to MIRCOP's demands. Aside from encrypting users' files, MIRCOP is similar to RAA in that it can steal users' passwords for several applications including Mozilla Firefox, Google Chrome, Opera, Filezilla, and Skype. Fortunately, security researcher Michael Gillespie has created a decryption utility that victims can use to regain access to their files for free. Instructions for how victims of the ransomware can use the decryptor are provided on Bleeping Computer's MicroCop Ransomware Help & Support forum.

