
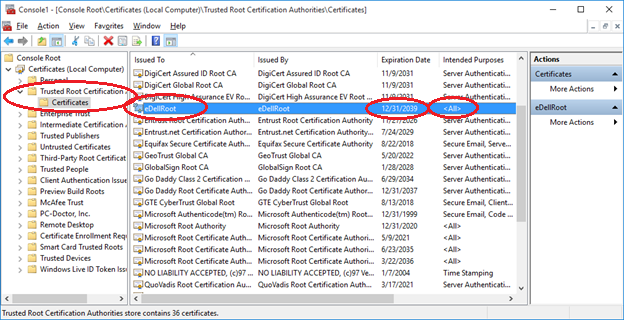
Dell Inc., a computer technology company, has provided instructions to customers on how they can remove a recently discovered root Certificate Authority (CA) from their laptops and PCs. On Monday, a Reddit user by the name of rotorcowboy posted a thread in which they explained how they had discovered a self-signed root CA called "eDellRoot" while troubleshooting another issue on their Dell XPS 15 laptop. Further investigation revealed not only that the root certificate came with a private key, a raw copy of which could be obtained using several tools, but also that this same exact certificate/private key combo had been pre-installed on every laptop shipped by Dell and that the CA could sign server certificates. These findings corroborate the findings of Joe Nord, a computer scientist who in a post on eDellRoot explains how the CA does not expire until 2039 and is more powerful than the DigiCert certificate also installed on Dell computers.
Source: Joe Nord If that were not enough, a detailed analysis by researchers at Duo Security reveals how eDellRoot will reinstall itself at boot if uninstalled using the Dell.Foundation.Agent.Plugins.eDell.dll module. Amidst observers' comparisons to Superfish, Dell released the following statement in an attempt to assuage people's fears:
"The certificate is not malware or adware. Rather, it was intended to provide the system service tag to Dell online support allowing us to quickly identify the computer model, making it easier and faster to service our customers. This certificate is not being used to collect personal customer information."
These reassurances notwithstanding, the reality is that attackers can leverage the CA to their advantage by setting up a malicious Wi-Fi hotspot in a public place, such as a cafe, and executing a man-in-the-middle (MitM) attack by intercepting Dell computers' traffic and stripping away the encryption, as noted by The Register. Dell has since announced that it is taking steps to remove the certificate from affected machines:
"We are providing our customers with instructions to permanently remove the certificate from their systems via direct email, on our support site and Technical Support. We are also removing the certificate from all Dell systems moving forward."
Customers can find instructions to manually remove the CA here. You can also check to see if your computer has eDellRoot installed by visiting this website.

