
The malware authors behind DMA Locker have outfitted the ransomware with numerous updates that advance its maturity. Malwarebytes researcher Hasherezade explains in a blog post that she first detected the crypto-malware variant back in January of this year. DMA Locker's first iterations were easily decryptable. Additionally, they could work offline, for the RSA public key involved in the encryption process came hardcoded in the ransomware's binary. All of that has changed. For starters, DMA Locker 4.0--the newest version--now uses a command and control (C&C) server, which means it requires Internet connectivity to function properly. Per Hasherezade's findings:
"[The ransomware] cannot encrypt files offline. It needs to download the public RSA key from its C&C. That’s why, if the file has been opened on the computer without the internet connection, it will just install itself and wait. If the machine is connected--it runs silently until it finish encrypting the files."
Once the ransomware has finished encrypting a user's files, it displays the following ransom message:
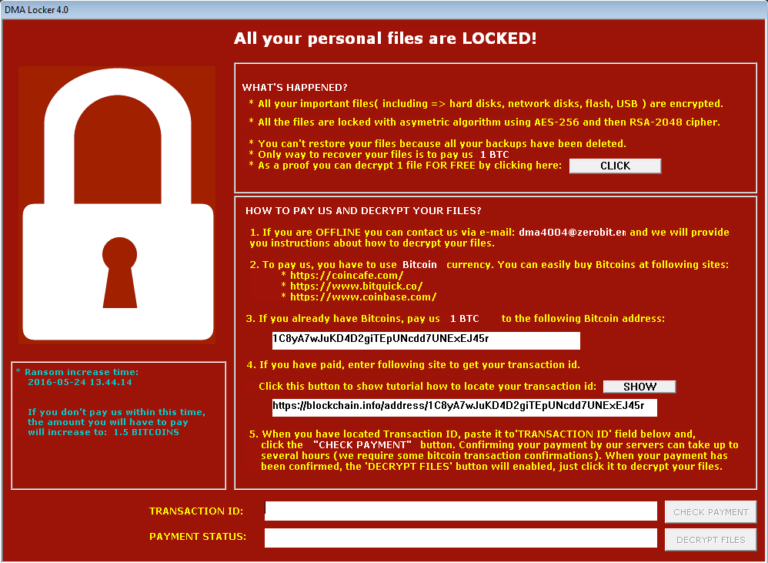
That note comes with a few usability improvements, including the ability to decrypt one file for free. A website provided by the ransomware for victims claims to offer that same service, but Hasherezade never received a decrypted file back after testing it. Strangely, that same website is hosted normally and not on Tor, which suggests it might still be under construction. But development is likely to continue. Unlike its earlier incarnations, DMA Locker 4.0 is packed in an underground crypter, which means security researchers and anti-virus products will have a harder time detecting it. That evasion tactic, when couple with its embrace of the Neutrino exploit kit for distribution, optimizes the ransomware for a large infection campaign:
"The recently observed changes suggest that the product is preparing to be distributed on a massive scale. Few important things got automated," notes Hasherezade. "Distribution is now exploit kit based--that makes it reach much more targets."
Users can protect themselves against an exploit kit attack leveraging DMA Locker by implementing vendor security updates as soon as they become available. For more ransomware prevention tips, click here. Users can also learn more about ransomware in general here.

