
The DoubleDoor Internet of Things (IoT) botnet circumvents firewall protection and other security measures by abusing two vulnerabilities. Detected by NewSky Security in its honeypot logs, DoubleDoor begins by deploying CVE-2015-7755. The vulnerability allows remote attackers to gain administrative access to ScreenOS, an operating system for Juniper Networks' hardware firewall devices, by entering a hardcoded password. In so doing, the attackers bypass authentication offered by those devices. After circumventing firewall protection, the botnet evades security measures offered by the ZyXEL PK5001Z Modem by exploiting CVE-2016-10401. Attackers can abuse this security weakness to gain root access if they know a non-root account password. To obtain those superuser privileges, DoubleDoor leverages a password-based attack to compromise an account with basic privileges.
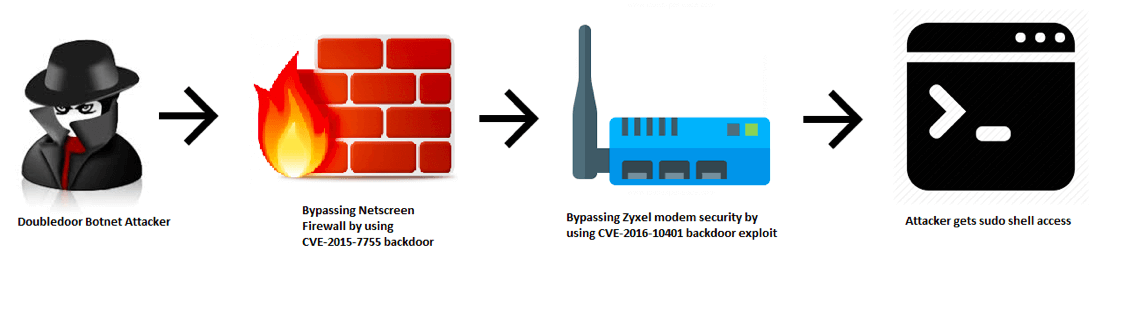
Source: NewSky Security NewSky found that DoubleDoor isn't unlike Mirai and other IoT botnets in that it attempts to invoke the shell with an invalid string to produce "{string}: applet not found," thereby confirming the attack has succeeded. Unlike other IoT-based threats, however, DoubleDoor doesn't use a static password for this procedure. NewSky's Ankit Anubhav explains:
DoubleDoor botnet takes care of this, by using a randomized string in every attack (as shown in the image below). Lack of any standard string will make sure it is not very easy to classify the recon activity as malicious. The strings have one thing in common though, they are always 8 in length.
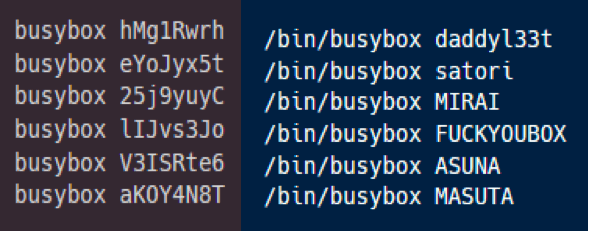
Randomized recon strings used by DoubleDoor at left vs “Easy to classify” strings used by prominent IoT botnets at the right. Anubhav and his fellow researchers detected DoubleDoor attacks only between 18 January and 27 January, with most of that malicious activity originating from South Korean IPs. Even so, NewSky anticipates DoubleDoor attacks will become more prolific in the future. With that said, it's important that organizations review their IoT security policies and implement a patch management program to manage vulnerabilities for their IoT devices and other IT assets. To learn how Tripwire can strengthen an organization's patch management strategy, click here.

