
American file hosting service Dropbox said a data dump of approximately 60 million users' records is real.

A spokesperson for the company said the records, which include email addresses as well as hashed and salted passwords, are the same as those affected by a security incident that occurred several years ago. In July 2012, the company discovered someone had stolen people's usernames and passwords from other sites and had abused those credentials to access a small number of Dropbox accounts. The file hosting service implemented a number of security updates in response to the incident. More recently, in mid-August 2016, it instituted a mandatory password reset for all users who haven't changed their passwords since 2012. As the spokesperson told The Register:
"We are confident that this is not a new incident; this data is from 2012, and these credentials were covered by the password reset."
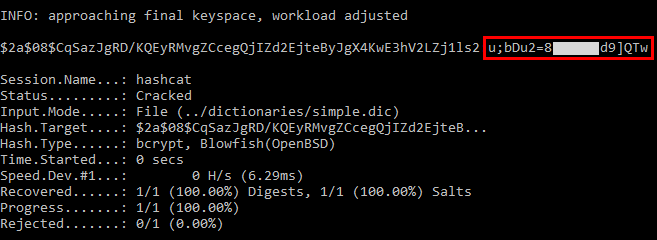
It's been a tough summer when it comes to "mega-breaches." In total, hackers stole hundreds of millions of user records from LinkedIn, Tumblr, and a bunch of other companies and then posted them for sale on the dark web. In the case of Dropbox, Motherboard reports it gained partial access to four files that together contain the account details for 68,680,741 accounts. 32 million of those accounts are protected by the hashing function bcrypt, which leaves little hope for attackers of cracking those accounts. The rest appear to be protected by SHA-1. Dropbox said all hashes are also protected by a salt, a random string which is added to the hashing process to further boost password security. On 31 August, security researcher Troy Hunt independently verified the legitimacy of the leaked files.
He's sent the records to the Have I Been Pwned? service and also reached out to some of the users. If you haven't changed your Dropbox password since mid-2012, please do so now. I would also recommend you set up two-step verification (2SV) so that you know your account is protected with an additional layer of security.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

