
A targeted email campaign used a fake Microsoft Silverlight update to trick users into installing a keylogger onto their computers. Overall, the attack campaign consisted of only a few malicious emails sent to employees at a major financial services provider. Each email bore a Microsoft Office document as an attachment--an attack vector seen in other campaigns. But unlike other attacks, the document did not leverage malicious macros. Proofpoint researchers explain in a blog post:
"The emails sent in this attack include a Microsoft Word attachment named 'info.doc'. The document contains an image requesting that users click to install Microsoft Silverlight to view the content .... Closer examination reveals that there are no macros in this document, but rather a 'Packager Shell Object Object' ...."
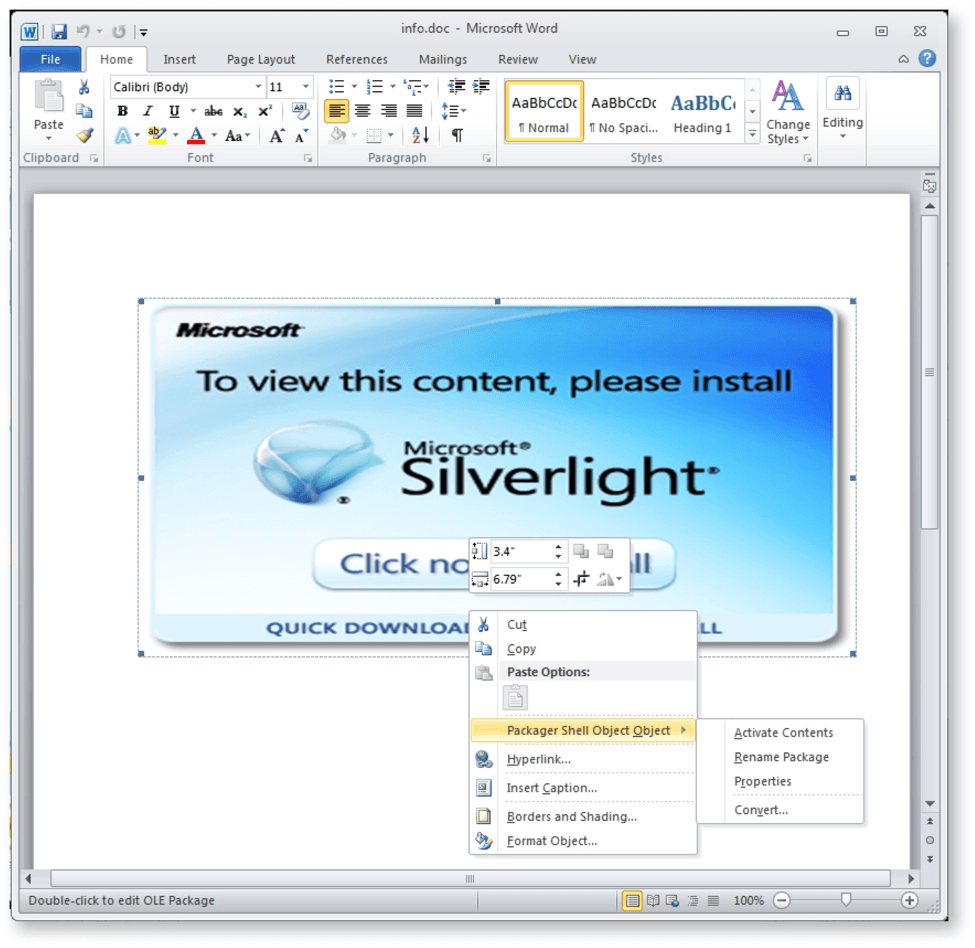
Right-clicking on the Silverlight update image in the lure document reveals that it is an embedded object instead of just a linked figure. (Source: Proofpoint) In actuality, the object is a Visual Basic Script file that attackers obfuscated by adding "We are safe" after every character in strings. Proofpoint's researchers quickly found a way to deobfuscate the file, however. As of this writing, the file is no longer available. But the research team retrieved a sample from Virus Total. Its analysis reveals the payload is capable of identifying the public IP address of an infected machine by placing a network request to http[:]//icanhazip[.]com. The malware also calls the "GetAsyncKeyState" Windows API multiple times a second, a feature which makes the payload a keylogger.
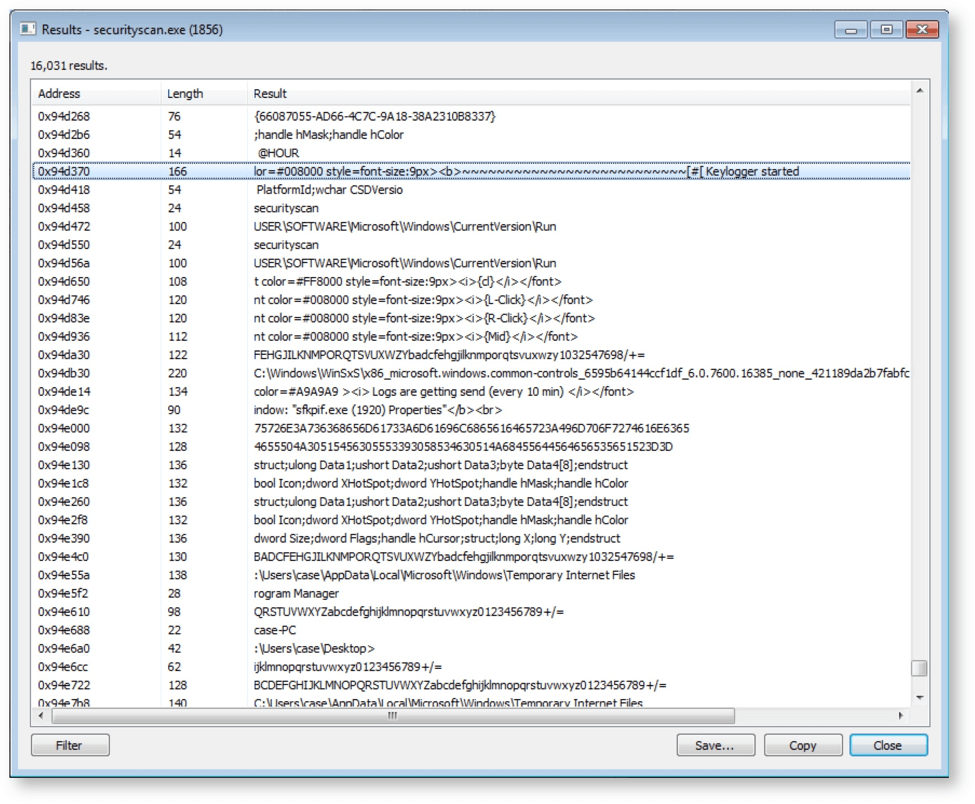
A memory dump of the Virus Total sample confirms keylogger function. (Source: Proofpoint) Proofpoint still has more to learn about this malware:
"To date, we have not identified this particular keylogger. It is written in AutoIt and uses additional tools such as the Lazagne password recovery tool that it downloads from hxxp://0v3rfl0w[.]com. The infection vectors are of greater interest at this point and the functions of the malware itself are fairly straightforward."
Ultimately, the keylogger sends all of the information it steals to two hard-coded Gmail accounts. Attackers love to use malicious macros to target users, but they also have other ways of infecting a machine. As a result, in addition to fighting macro-based malware, organizations should take steps to help their employees spot suspicious emails and attachments. They should also use email filters to block malspam outright.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

