
A "Facebook password stealer" is capable of covertly pilfering sensitive information from any wannabe attacker who uses it. On 3 August, a security researcher by the name of MalwareHunterTeam tweeted about the credential-collecting tool's hidden nature. https://twitter.com/malwrhunterteam/status/893053328057413634 The phrase "how to hack facebook account" yields plenty of results in popular search results. Google returned more than 15 million of them in less than a second of scanning the public web. Who knows how many results that either the deep web or dark web yields?
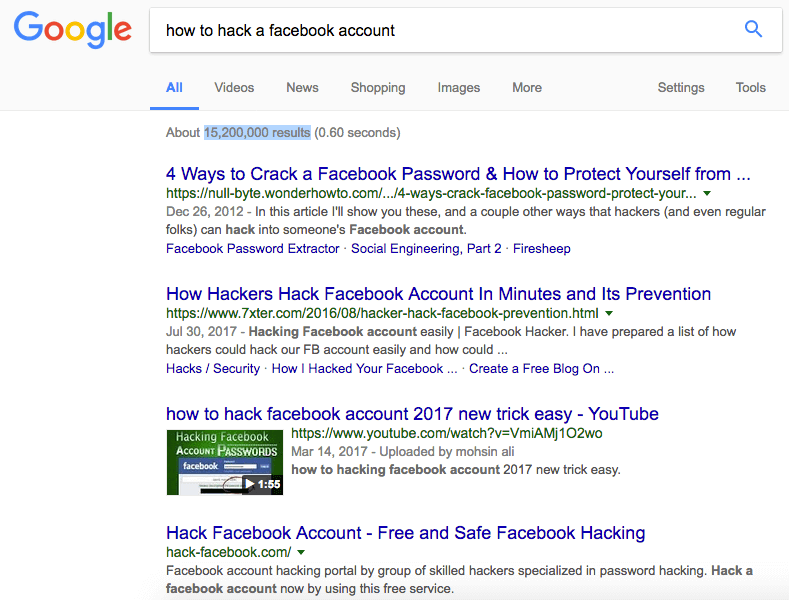
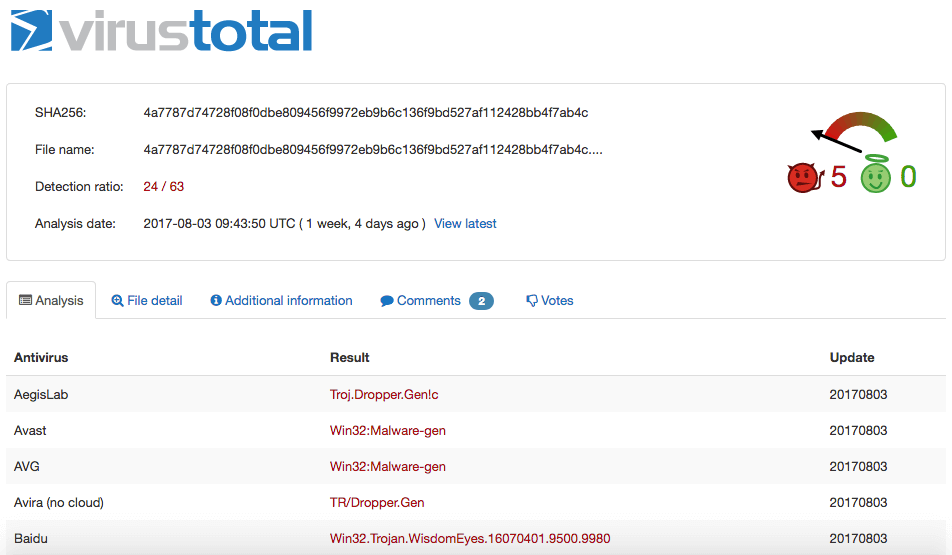
Screenshot of "how to hack a facebook account" Google search results on 14-08-17. With that said, it comes as no surprise that computer criminals would seek to capitalize on wannabe attackers' interest in cracking a target's Facebook account. Upon successful installation onto a bad actor's computer, this utility loads up njRAT, a remote access tool. The malware, which also goes by the name Bladabindi, has been around since at least 2013 when researchers at Fidelis Cybersecurity Solutions detailed in a report its indicators, domains, and Tactics, Techniques, and Procedures (TTPs) used for some of its active attack campaigns. News surrounding njRAT became scarce in 2014. But then the malware resurfaced in 2015 and helped inspire the creation of more sophisticated RATs. Bladabindi can assume remote control of a device, collect information about the infected machine, open a remote shell into the command line, record the computer's microphone and webcam, log keystrokes, and (perhaps ironically) steal passwords, among other functions. A
This isn't the only time or social networking platform that digital attackers have targeted in such a manner. Back in April 2016, a spam campaign targeting would-be Twitter crackers came to light. The ruse generates a "pass.txt" file after an actor enters in a targeted Twitter handle. But before they can read the fake file claiming to contain a target's Twitter password, aspiring hackers have to first fill out a survey, download potentially malicious files, or even provide the credentials for their own Twitter account. The takeaway of these misleading password stealers is obvious: don't be a computer criminal! Not only is searching how to hack another person's account ethically wrong, but it can also expose the user to malware and opportunistic attacks. Instead of trying to hack other people, users should protect their accounts against hackers by enabling two-step verification (2SV) and by creating a strong password using these tips.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

