
Fraudsters are leveraging an emerging social engineering technique called "angler phishing" to fool victims into handing over their PayPal credentials. Researchers at security firm Proofpoint, who discovered this particular campaign, elaborate on what sets angler phishing apart from ordinary phishing attacks:
"The attack technique takes its name from the anglerfish, which uses a glowing lure to entice and attack smaller prey. In an angler phishing attack, a fake customer-support account promises to help customers, but instead attempts to steal credentials. Social media angler phishers create fake customer support accounts that target customers of a wide variety of industries, but we have seen a majority of angler phish attacks focus on customer support accounts for financial services brands."

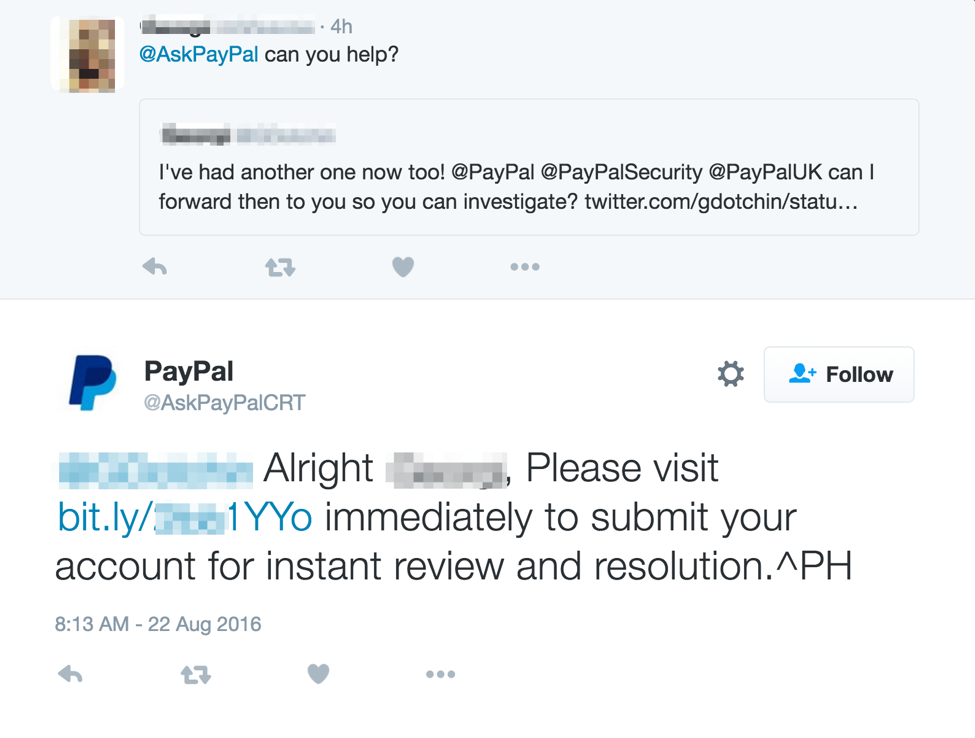
It's not the first time researchers have run into an angler phishing attack. Back in August, Malwarebytes came across scammers targeting Natwest bank customers on Twitter. Perhaps that campaign inspired other angler phishers to cast their lines out. According to Proofpoint, this newest scam begins when a user directs a tweet to PayPal's official Twitter handle (@PayPal). Fraudulent PayPal accounts with a convincing handle of their own, like @AskPayPal_Tech and @AskPayPalCRT, monitor PayPal's legitimate account for an opportunity to target customers awaiting a response. If circumstances permit, they inject themselves into the conversation and try to persuade users to click on a shortened link for further assistance.
Clicking on that link redirects users to a convincing log-in page that bears PayPal's brand. But don't be fooled! It's fake, and it's only seeking to steal users' credentials.
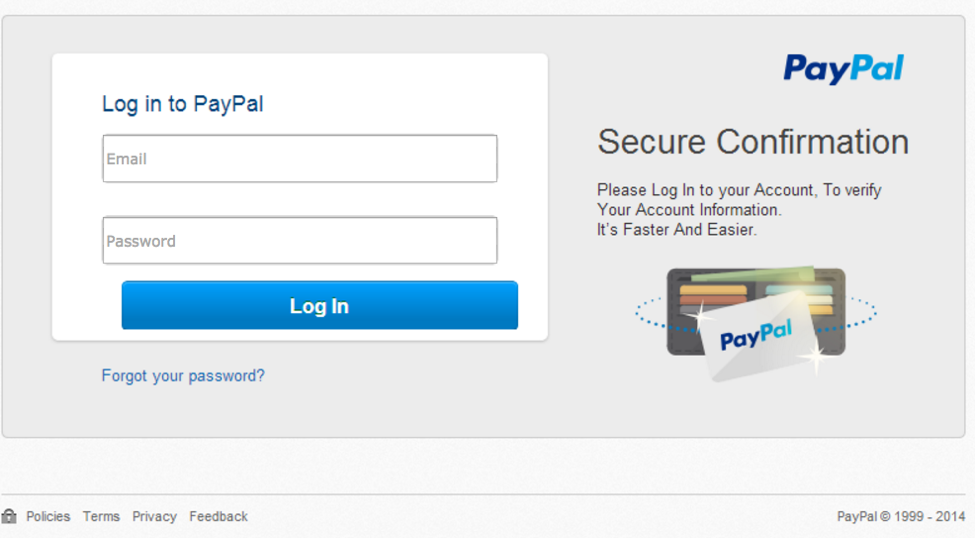
Fake site with stolen branding, which is directed from the angler phishing attack on the AskPayPal_Tech account (Source: Proofpoint) Proofpoint recommends companies like PayPal work to block angler phishing attacks by monitoring social media and looking for fake accounts, particularly those that are created during non-business hours. In the meantime, users can protect themselves against angler phishing by communicating only with a company's official Twitter handle. Fake support accounts likely won't have many tweets to their name, and they will leverage only shortened links to hide the true destination of their URLs. Users should also consider implementing two-step verification (2SV) if they wish to protect their accounts with an additional layer of security.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

