
Attackers are using fake encrypted PDF documents to try to phish for unsuspecting users' login credentials. John Bambenek, a handler at SANS Internet Storm Center, disclosed the phishing campaign on 4 January. He found that the offending fraudsters are targeting users who lack a high level of security awareness. As he told Threatpost:
"This is an untargeted phishing campaign. They are not going after the most sophisticated users. They are going after Joe Cubicle that may not think twice about entering credentials to unlock a PDF."
The campaign begins when a target receives an email from a school domain. Each attack email comes with the subject "Assessment document" and a PDF document. The attached document claims to contain a link regarding Vet Meds, a brand of medication for pets.
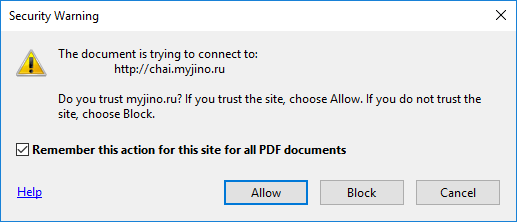
Source: SANS Internet Storm Center That couldn't be further from the truth. The document actually links to a Russian website for a transaction with the Society for Worldwide Interbank Financial Telecommunications (SWIFT), a banking network which saw its fair share of heists in 2016. Bambenek provides more details in an Internet Storm Center alert:
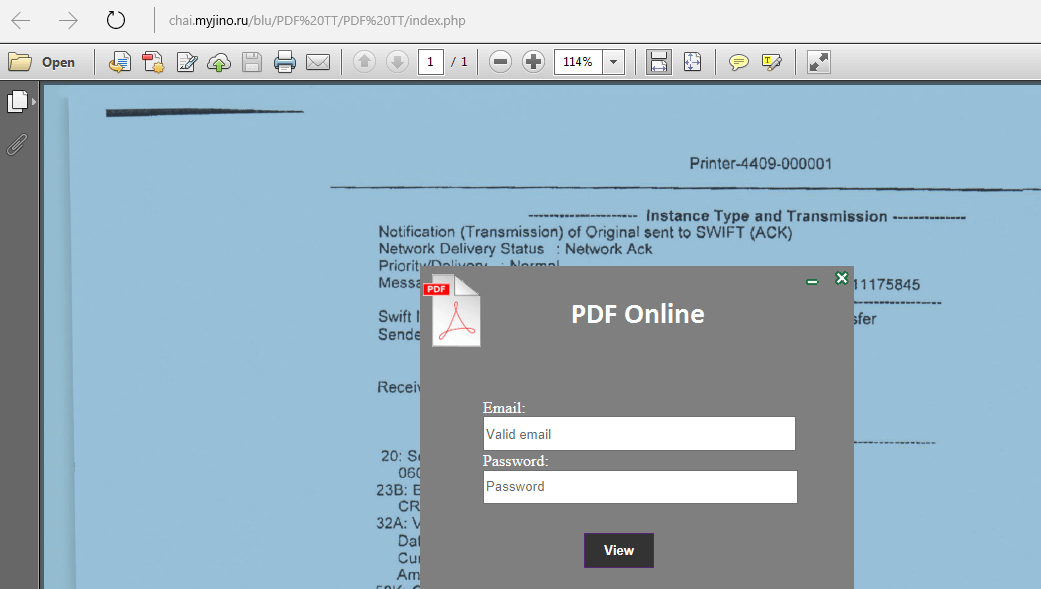
"The PDF itself was created with Microsoft Word and included a link that suggested it was a locked document and you needed to click a link to unlock it which pointed to chai[.]myjino[.]ru and gave a screen with a purported PDF behind it and a login box that it happily accepts."
Source: SANS Internet Storm Center This phishing campaign isn't picky when it comes to a victim's login credentials. Any username and password combination will do. In fact, the fake login box will send over any information a user inputs into its two designated text fields.
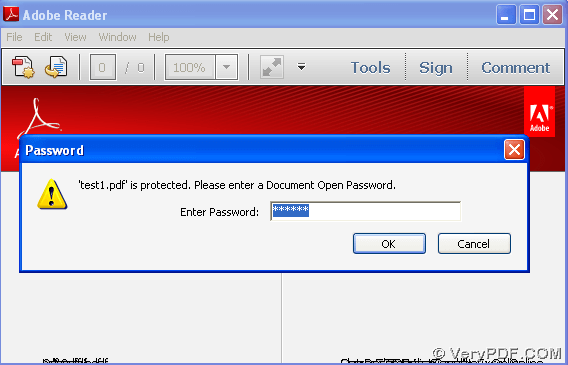
Source: SANS Internet Storm Center Users can protect themselves against this campaign and others like it by looking for tell-tale signs that give the scam away. First, they should notice that the Russian website does not match up to the school's domain, a discrepancy which could suggest someone compromised an email account belonging to the latter. Second, they should know that legitimate encrypted PDF documents will never ask for a user to enter any of their account credentials in order to authenticate themselves. Instead it'll ask for a password that's usually unique to that particular document. It'll look something like this:
Finally, users should in general refrain from clicking on suspicious links and email attachments.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

