
Security researchers have released a free decryption utility which victims of Ims00rry ransomware can use to recover their files. On 12 July, anti-virus and anti-malware solutions provider Emsisoft made the decryptor available to the public. The firm published a follow-up post about is tool two days later.
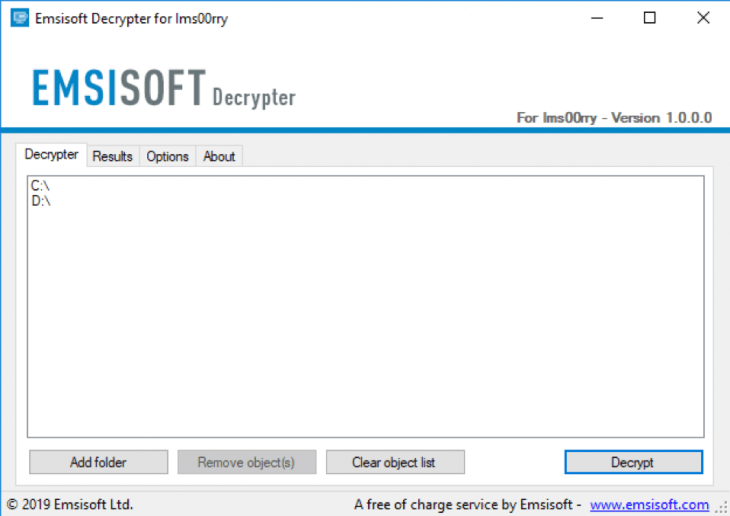
Emsisoft's Ims00rry decryptor In its research, Emsisoft explains that Ims00rry leverages AES-128 to encrypt users' files. It doesn't add an extension to each encrypted file once it's done, however. Instead, it adds “—shlangan AES-256—” to each affected file's contents. After completing its encryption routine, the ransomware saves a ransom note to each infected machine. This note instructs victims to contact the digital attackers via the Telegram bot @Ims00rybot so that they can pay $50 in exchange for the decryption software. Here's the exact text of the ransom message, as provided by Emsisoft:
I am sorry!!! My friend. I want to start my own business, but i have no money. All your files photos, databases, documents and other important are encrypted with strongest encryption and algorithms RSA 4096, AES-256. If you want to restore your files payment and write to Telegram bot Price decrypt software is $50. Attention!!! Do not rename or move the encrypted files. Bitñoin wàllet: 1tnZbveCXmqRS1gfZSxztG5MbdJhptaqu Contact Telegram bot: @Ims00rybot
Emsisoft is urging victims of Ims00rry to not pay the ransom and to use its decryptor instead. The emergence of this decryption tool highlights security researchers' ongoing efforts to thwart ransomware attackers. Organizations can help these experts in their work by making it as difficult as possible for bad actors to successfully infect their workstations with ransomware. To do this, they should follow these steps designed to prevent a crypto-malware infection in the first place. They should also invest in a solution that's capable of defending their systems against known malware as well as zero-day malware attacks. Learn how Tripwire Malware Detection can assist in this regard.

