
Two malware families known as GootKit and Godzilla are closing out the year strong with separate campaigns designed to harvest users' financial information. In Canada, the GootKit trojan is targeting members of several financial institutions. The campaign begins when a user receives a spam message that appears to have originated from a trusted actor like the local postal service. The message tells the recipient they need to open an Office document to view a bill or schedule a package's delivery. But it's a fake. The attachment comes with malicious macros which, when enabled by the user, downloads Gootkit onto their computer. Spam mail isn't the only distribution vector for GootKit in this campaign, however. The trojan has also embedded itself into a pseudo-Darkleech infection that leverages the Nemucod malware downloader to install Cerber ransomware. Researchers first spotted GootKit in 2010. Since then, its developers have expanded its range of capabilities to include downloading additional malware onto an infected computer, creating backdoors, and stealing sensitive and financial information. The malware's command and control (C&C) server even includes information on how much money its developers think they can harvest from each victim.
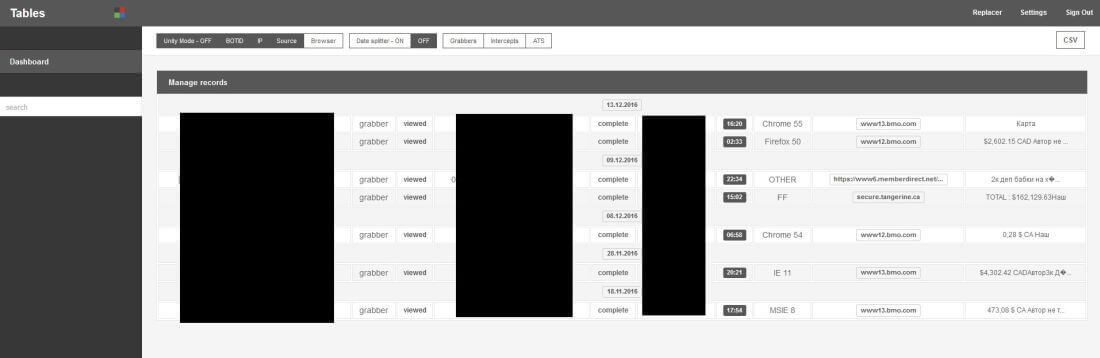
GootKit's C&C. (Source: Heimdal Security) While GootKit makes its rounds in the Great White North, Godzilla Loader is also using spam mail to target users' financial information. In this campaign, users receive what appears to be an email about their income tax refund notice. The message comes with an attached Word document that contains malicious macros. Clicking on the document and enabling content triggers a PowerShell command that downloads Godzilla. As of this writing, the document isn't well known, as it's detected by only 13 of 56 anti-virus providers on VirusTotal.
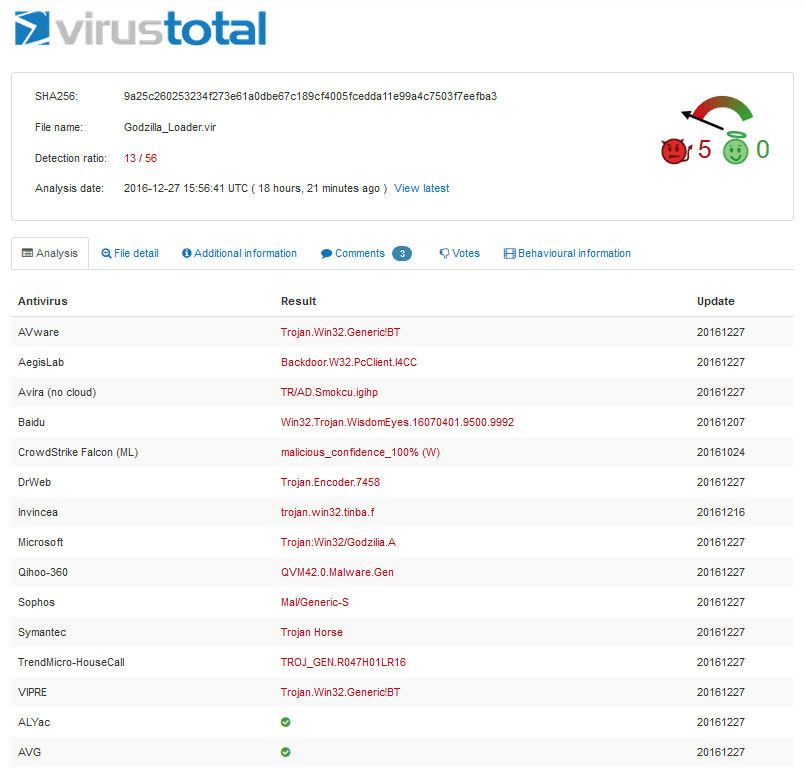
Detection rate of malicious document containing Godzilla Loader, as of 29 December 2016 at 07:00 EST. (Source: VirusTotal) Heimdal Security's security evangelist Andra Zaharia explains in a blog post what happens upon successful infection:
"Once Godzilla infiltrates the system, it will connect to several Command & Control servers to upload the financial information it has harvested from the compromised system."
The malware, which was discovered in May 2016 and which is known to load up malware like TrickBot onto an infected machine, also retains the right to issue commands to the compromised computer via its C&C. A login screen for Godzilla's C&C interface is shown below.
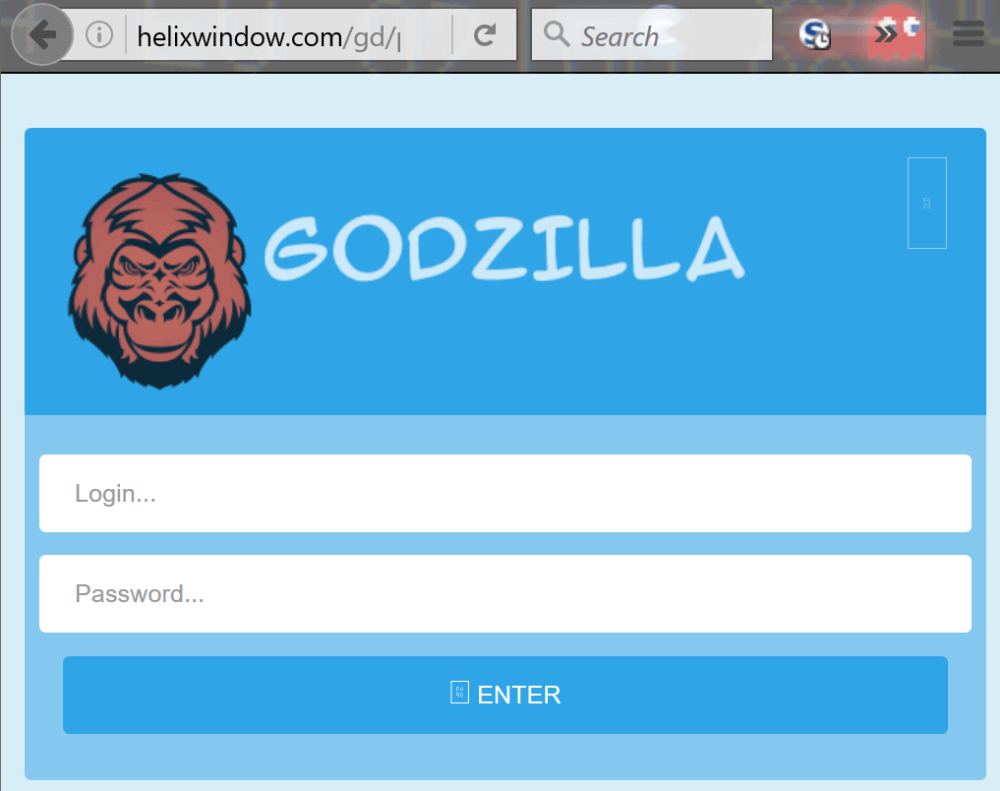
Godzilla login screen. (Source: Heimdal Security) Both of these campaigns illustrate the importance of users refraining from clicking on suspicious links and email attachments. Users should also make sure they've disabled Office macros by default. They can learn how to do so here.

