
GoldenEye ransomware wants to interview with your company's HR department, but it's not interested in filling an open position. For this new campaign, GoldenEye has assumed a job application theme to target German speakers in companies' HR departments. The authors of the ransomware, which is an updated form of Petya, know it's part of HR employees' job to open attachments from unknown individuals. They find no issue with abusing that behavior to get what they want. The Check Point Research Team explains the campaign begins when an HR employee receives a job application email containing two attachments:
"The first attachment is a PDF containing a cover letter which has no malicious content and its primary purpose is to lull the victim into a false sense of security. The second attachment is an Excel file with malicious macros unbeknown to the receiver. It contains a picture of a flower with the word 'Loading…' underneath, and a text in German asking the victim to enable content so that the macros can run."
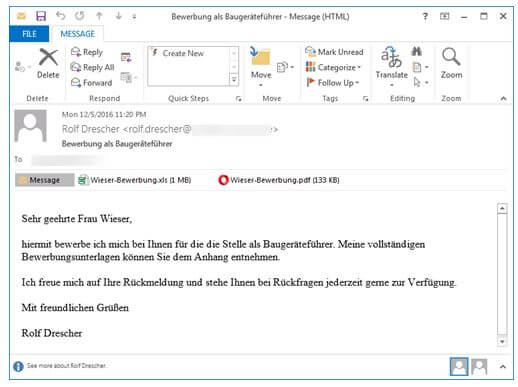
Screenshot of the email (Source: Check Point) If the recipient enables content, the malicious code embedded in the macro executes the ransomware payload. GoldenEye gets to work encrypting the user's files. Once its encryption algorithm has done its work, the crypto-malware displays its ransom note. But GoldenEye is just getting started. As an updated form of Petya, the ransomware has the ability to replace the Master Boot Record and encrypt the Master File Table (MFT) so long as it gains administrative privileges. With those superuser rights, the ransomware can prevent the computer from loading the operating system correctly and from discovering the locations of all files. That's unfortunately the way it goes in this campaign. As Check Point notes:
"After displaying the ransom note, GoldenEye forces a reboot and starts encrypting the disk. This action makes it impossible to access any files on the hard disk. While the disk undergoes encryption, the victim sees a fake “chkdsk” screen, as in previous Petya variants."
After it's encrypted the disk, GoldenEye loads up its boot-level ransom note and demands the victim pay 1.3 Bitcoins (approximately 1435 USD as of this writing).
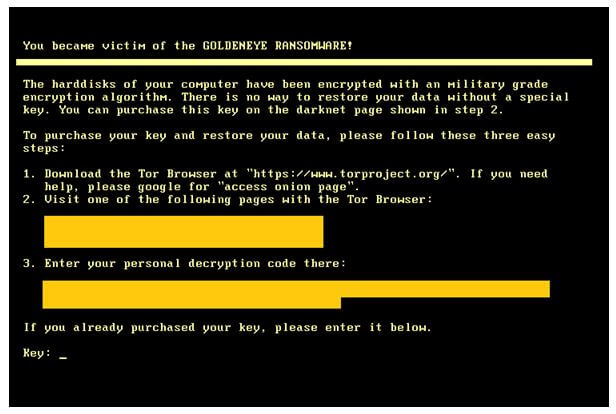
GoldenEye's boot-level ransom note (Source: Check Point) This campaign, which mimics activity previously exhibited by another evolving crypto-malware family named Cerber, presumes unsuspecting HR employees will enable content in the Excel document. While those in HR should expect to receive emails from all kinds of people, they shouldn't give anyone who sends a Microsoft Office document with macros enabled the time of day. In fact, organizations should make sure that every computer in every department disables Office macros by default. They should also invest in other strategies designed to prevent a ransomware infection.

