
A hospital located in Southern California has paid $17,000 for the restoration of its system following a ransomware attack. News first broke last week about how staff at the Hollywood Presbyterian Medical Center began noticing issues in the hospital's IT system in early February. The Center decided to temporarily suspend its computer system, which resulted in several departments being shut down, patients being diverted to other hospitals for treatment, and registrations/log-ins being processed via paper and fax. One doctor who wished to remain anonymous told reporters that ransomware was to blame for the IT issues and that the attackers were demanding 9,000 BTC (approximately $3.6 million) in payment for the restoration of the hospital's data. A statement issued by the hospital on Wednesday reveals, however, that while ransomware was indeed behind the interruptions, the attackers had asked for only 40 Bitcoins ($17,000). After working with law enforcement, Hollywood Presbyterian decided to pay that demand.
"HPMC has restored its electronic medical record system ('EMR') on Monday, February 15th," explains Allen Stefanek, president and CEO of the medical center. "All clinical operations are utilizing the EMR system. All systems currently in use were cleared of the malware and thoroughly tested. We continue to work with our team of experts to understand more about this event."
Computer forensics experts involved in the case have determined that the "Locky" ransomware, a "masterpiece of criminality" that is spread via spam phishing emails, had infected the hospital's system.
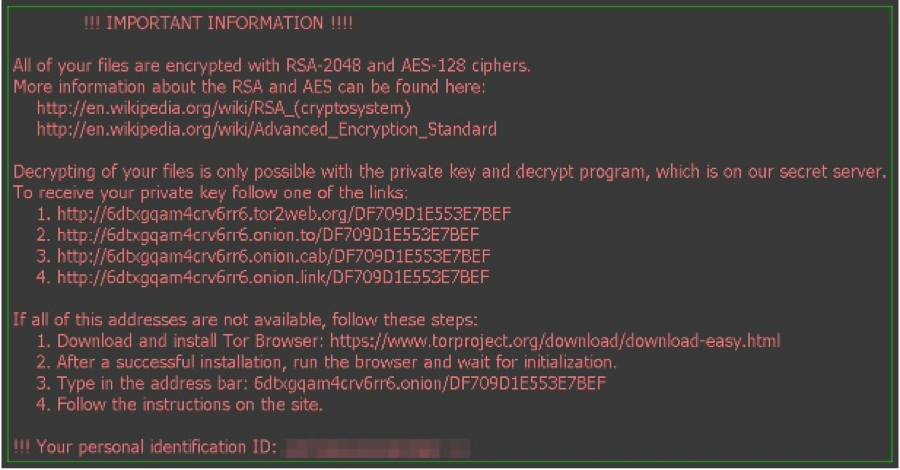
The Locky malware ransom note (Source: Palo Alto Networks) Palo Alto Networks' researchers have observed the ransomware in 446,000 unique sessions thus far. However, with some indicating that the malware is infecting up to 90,000 victims per day, that number is sure to increase over the coming weeks. Regular data backups, caution around suspicious email attachments, and an updated antivirus solution are all useful when it comes to preventing a ransomware infection. For more tips on how you can avoid falling victim to this type of malware, please click here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

