
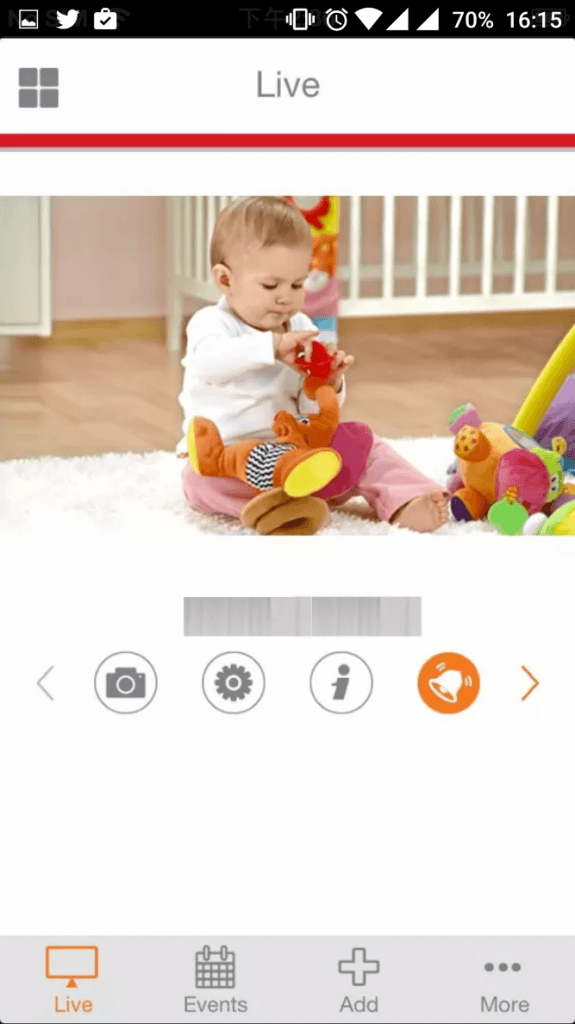
Actors can use spoofing attacks to gain control of a smart webcam that leaks its own password as well as local network credentials. To raise awareness about the insecure design of many Internet of Things (IoT) devices, researchers at Bitdefender Labs took a look at a smart webcam. The camera comes with a motion and sound detection system, two-way audio, and a built-in microphone and speaker. Those features allow it to function as a surveillance system or baby monitor. The product's installation process is pretty routine for smart devices. As Bitdefender explains:
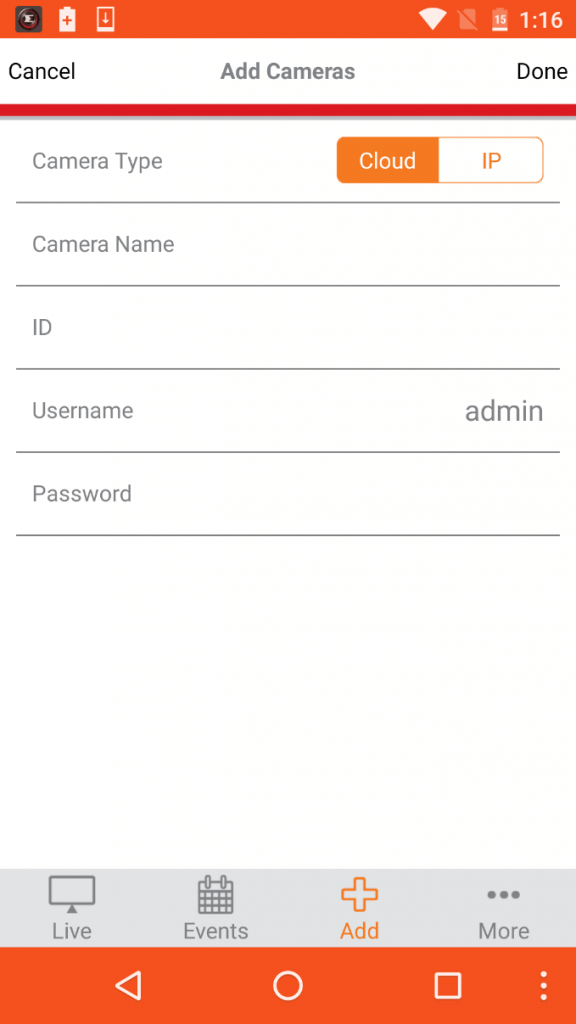
"The device follows the standard setup routine, creating a hotspot during configuration via a wireless network. Once installed, the corresponding mobile application tries to establish a connection with the device’s hotspot and after it detects it, the app connects to it automatically. Next, the app asks the user to introduce the credentials of his home network, which it transmits to the device. The smart plug connects to the local network and the setup process is complete."
So what's the problem? Here's a breakdown of some of the most pressing issues:
- The hotspot isn't password-protected, meaning anyone can connect to it.
- The device's infrastructure doesn't use robust security or authentication measures. For example, the app remotely connects to the device via a generally insecure authentication method known as Basic Access Authentication. Additionally, the device's username and password are not encrypted but encoded using a Base64 scheme when sent over the wire. That means an attacker could reverse the process to access the camera, change the login settings, and shut out the user.
- The mobile app sends the local network credentials over to the device in plaintext, meaning an actor could eavesdrop on that communication and gain unauthorized access to the user's Wi-Fi network.
- The webcam authenticates with its cloud server using its MAC address only. An attacker could therefore use another device with the same MAC address to impersonate the genuine product, intercept login information, and gain access to the device through the mobile app.
The final issue discussed above is particularly concerning given the camera's intended use. Bitdefender anti-malware researcher George Cabau elaborates on that point:
"Anyone can use the app, just as the user would. This means turning on audio, mic and speakers to communicate with children while parents aren’t around or having undisturbed access to real-time footage from your kids’ bedroom. Clearly, this is an extremely invasive device, and its compromise leads to scary consequences."
Nowhere in the blog post do the researchers name the product or the vendor. They do say, however, that they practiced responsible disclosure and that the vendor is currently working to fix the camera's security flaws. In the meantime, both users and manufacturers should do more to emphasize the importance of IoT security. Users should ask themselves questions about the devices they own and want to buy in order to select the most secure products out there, while manufacturers should implement better update mechanisms in their products. For additional perspective on the security challenges of the Internet of Things, please read this conversation.
Zero Trust and the Seven Tenets
Understand the principles of Zero Trust in cybersecurity with Tripwire's detailed guide. Ideal for both newcomers and seasoned professionals, this resource provides a practical pathway to implementing Zero Trust, enhancing your organization's security posture in the ever-evolving digital landscape.

