
Malicious actors began exploiting a patched critical vulnerability found in Joomla—a popular open-source content management system—just four hours after its details were disclosed. Discovered by researchers at Trustwave, the SQL injection flaw (CVE-2015-7297, CVE-2015-7857 and CVE-2015-7858) found in versions 3.2 through 3.4.4 of Joomla could potentially grant attackers full administrative access to any vulnerable site.
“CVE-2015-7857 enables an unauthorized remote user to gain administrator privileges by hijacking the administrator session. Following exploitation of the vulnerability, the attacker may gain full control of the web site and execute additional attacks,” explained the researchers in a blog post.
Hours after the release of version 3.4.5 and Trustwave published a technical overview of the vulnerability, web security firm Sucuri reported direct attacks against two highly trafficked Joomla sites using its network. “What is very scary to think is that neither of these sites were patched at the time. The disclosure happened on a Thursday afternoon (evening in Europe), when many webmasters were already off for the day,” said Daniel Cid, Founder and CTO of Sucuri. Within less than 24 hours of the initial disclosure, the firm says it observed Internet-wide scans trying to hit every site on its network. “The first one was just a simple request, not an actual exploit, looking for the default Joomla SQL syntax error page,” explained Cid.
“If the SQL error page showed up, they knew the site was likely a viable target for a follow-up exploitation. The second request was trying to get the admin user form the jos_users table,” he added.
According to Cid, most of the IP addresses the firm flagged in these attacks were behind the Tor network. The number of exploit attempts spotted by Sucuri continued to increase significantly the following days, currently reaching more than 12,000 daily hits per day, said the firm.
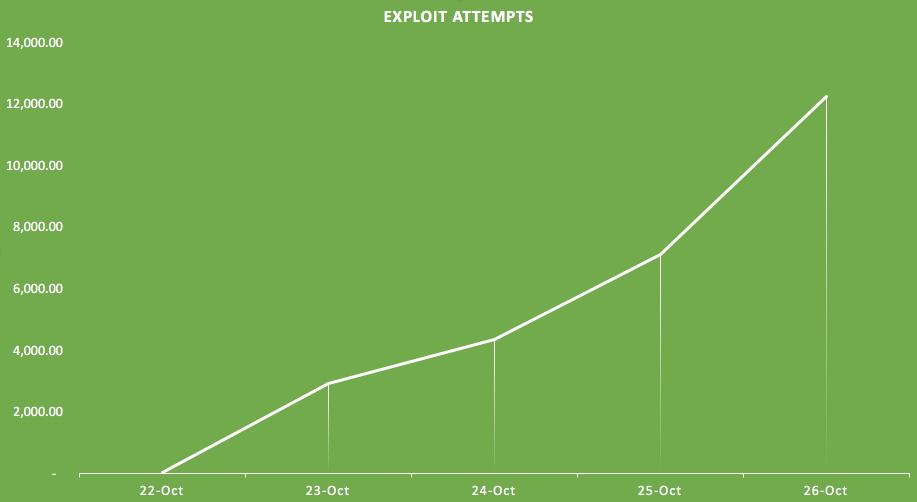
Source: Sucuri “This data tell us is that the average webmaster has less than 24 hours to patch a site after a serious disclosure like this. That’s for the average site (small to medium size),” warned Cid. For popular sites, webmasters likely only have a couple of hours, from disclosure to attack, making it critical for them to react fast.
“This is why we emphasize the importance of Defense (security) in Depth. You can not just rely on being updated as your only layer of security. With the proper access control, monitoring, Intrusion detection and prevention system, you can be ahead when cases like this happen or even a 0-day exploit,” Cid concluded.
As of October 27, 2015, W3Techs estimates Joomla to have 6.6 percent share of the market for website content management systems. Furthermore, Internet services company BuiltWith estimates that more than 2.8 million websites worldwide use Joomla.

