
A backdoor espionage trojan known as Kazuar has API access that it can leverage to run commands on the systems it compromises. The malware, which is written in Microsoft's .NET Framework and uses the ConfuserEX open source packer, initializes by gathering system and malware information and using those items to generate a mutex. It then creates a series of folder groups, including "sys" for storing configuration settings and "plg" for plugins that extend the trojan's functionality. Throughout this setup process, it logs debugging messages to its "log" folder. Once initialization is complete, Kazuar follows one of four execution paths. Its main entry point specifies the malware to install itself as a service, to inject itself into the explorer.exe process if it detects it's running on a machine running Windows, or to run the method containing its functional code if it detects a Unix or Mac environment. From there, it attempts to establish persistent access on the machine, contacts its command and control (C&C) server, and upon successful connection transmits an action identifier to its C&C that corresponds with one of a series of commands.
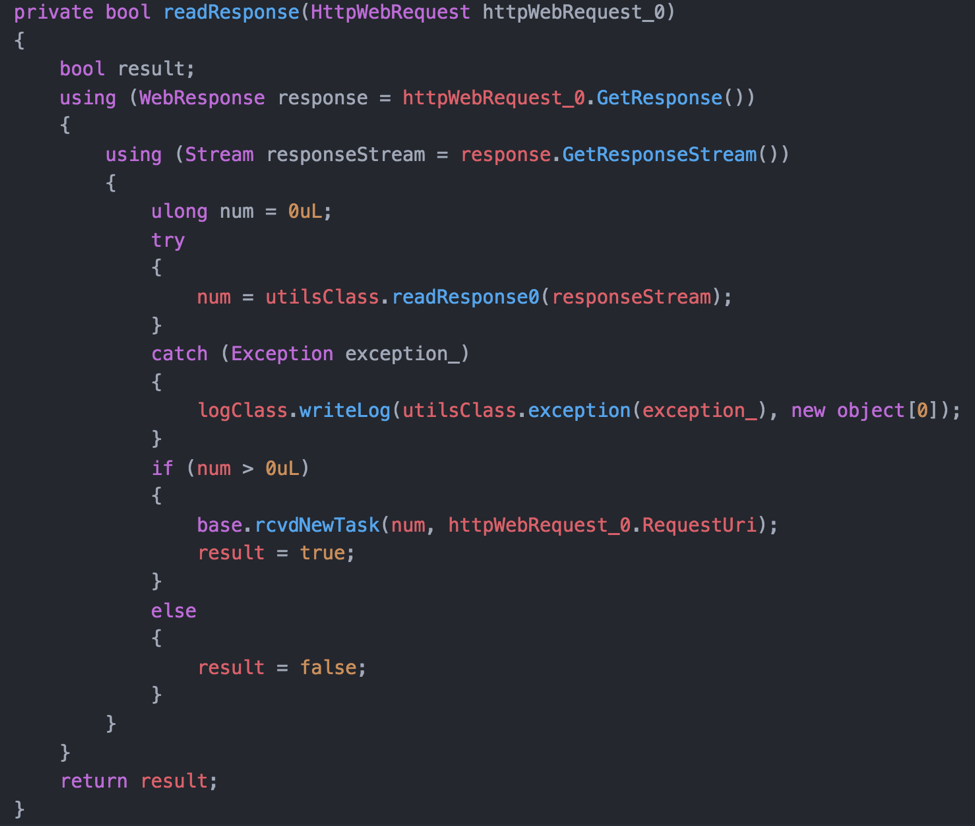
The response parser listens for new tasks to be received from the command and control server. (Source: Palo Alto Networks) Some of these instructions allow the malware to capture screenshots or take an image from an active webcam. Others allow it to gather system information or copy files. But one command in particular stands out. Brandon Levene, Robert Falcone, and Tyler Halfpop of Palo Alto Networks' Unit 42 threat research team identify that feature in a blog post:
"While many backdoor Trojans have extensive command handlers and plugin frameworks, Kazuar’s 'remote' command provides a functionality that is rarely seen in backdoors used in espionage campaigns. This command instructs the Trojan to start a thread to listen for inbound HTTP requests, which effectively turns Kazuar into a webserver. This functionality provides an API for the Trojan to run commands on the compromised system."
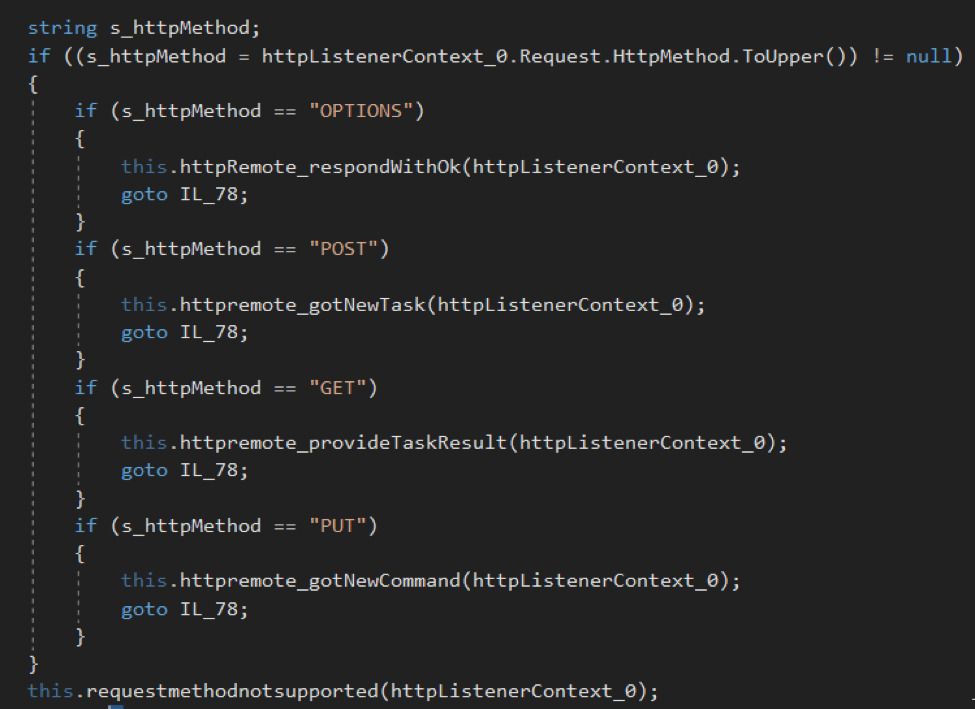
HTTP method handler used by Kazuar to provide threat actors with API access. (Source: Palo Alto Networks) The "remote" command essentially flips Kazuar's relationship with its C&C in that the latter begins sending requests directly to the former. Such functionality helps the malware avoid detection if the compromised asset is a remotely accessible server that might raise red flags when initiating outbound requests. Threat actors could also leverage the API access to create one accessible server as a location for exfiltrating an infected machine's data. As of this writing, Unit 42 is currently investigating ties between Kazuar and the Turla threat actor group. Some evidence suggests the attackers began using the malware as a replacement for another tool of theirs named Carbon. But researchers still have yet to confirm if Kazuar is indeed Turla's new second-stage backdoor.

