
Kentucky Fried Chicken (KFC) has told members of its Colonel's Club to change their passwords following an attack against its website. The fast food giant confirmed that the attack affected only Colonel's Club users. The loyalty program allows its 1.2 million registered members to collect Chicken Stamps and exchange them for rewards like meals. KFC revealed the attackers gained access to only 30 accounts and that they didn't make off with any personal information. But in the interest of security, it sent out an email to all Colonel's Club members urging them to change their passwords.
"Our monitoring systems have found a small number of Colonel’s Club accounts may have been compromised as a result of our website being targeted. Whilst it’s unlikely you have been impacted, we advise that you change your password as a precaution. If you use the same email address and password across other services, you should also reset them, just to be safe."
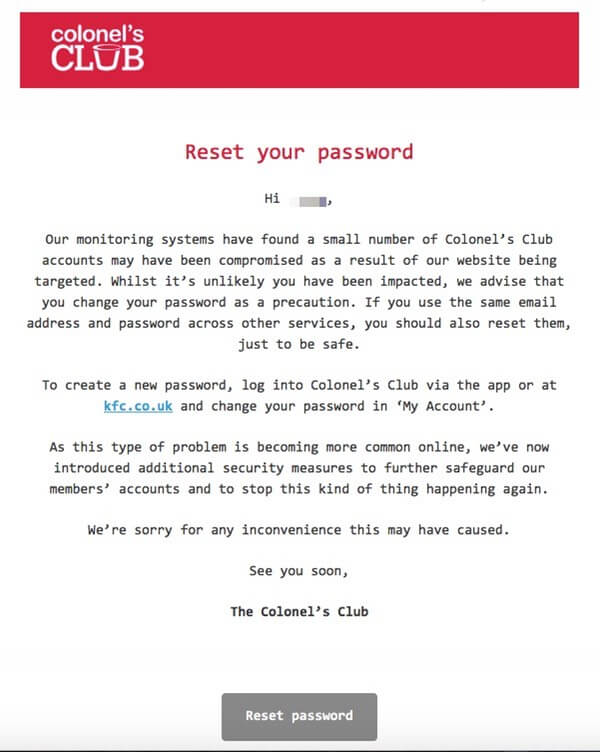
KFC password reset email (Graham Cluley)
Now let's be clear about something. KFC members who reuse their password across multiple services shouldn't change it just because of this attack. They should do so because it's good password security.
Attackers are banking on the fact that users protect multiple accounts with the same password. If they obtain a single set of credentials, they'll try authenticating the user across other services to see if they can gain access. It's called a password reuse attack, and it's something against which Carbonite, GitHub, and others tried to protect their users in 2016 following the mega-breaches at LinkedIn and Tumblr.
If you are a KFC Colonel's Club member, make sure you follow these recommendations when choosing a strong, unique password for each of your web accounts.
In the meantime, KFC said it's introduced "additional security measures" to protect members and "stop this kind of thing from happening again." It also apologized for the inconvenience that this incident might have caused users.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

