
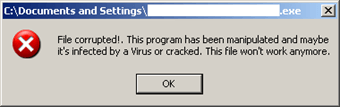
A new malware family named Alice is lean, mean, and designed solely to empty the safe of ATMs. Researchers at the Los Angeles security software company Trend Micro first discovered Alice in November 2016. It appears to have been in the wild since October 2014. Alice makes use of several evasive techniques to avoid detection. First, it follows the example of GreenDispenser and other ATM malware in its decision to use a commercial, off-the-shelf packer/obfuscator. The variant analyzed by Trend Micro used software called VMProtect to ascertain whether the embedded binary is running inside a debugger. If the check comes back positive, it displays an error message. Otherwise, it moves onto its next technique.
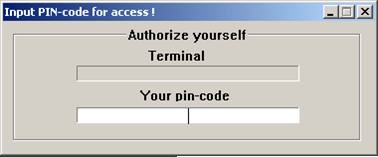
Source: Trend Micro Prior to executing, the malware looks for two registry keys associated with a legitimate Extensions for Financial Services (XFS) environment. Those keys' presence determines whether Alice displays an authorization window for a PIN code or another error message.
Source: Trend Micro
Source: Trend Micro Trend Micro senior threat researchers David Sancho and Numaan Huq elaborate on the significance of the PIN code for Alice-based attacks:
"Alice’s user authentication is similar to other ATM malware families. The money mules that carry out the attacks receive from the actual criminal gang(s) the PIN needed. The first command they enter drops the cleanup script, while entering the machine-specific PIN code lets them access the operator panel for money dispensing. "This access code changes between samples to prevent mules from sharing the code and bypassing the criminal gang, to keep track of individual money mules, or both. In our samples the passcode is only 4 digits long, but this can be easily changed. Attempts to brute-force the passcode will eventually cause the malware to terminate itself once the PIN input limit is reached."
Access to a PIN prior to emptying a target ATM suggests Alice is used only for in-person attacks. Infection could proceed by the money mules opening an ATM, inputting a malicious USB or CD-ROM, and operating the malware through a keyboard that connects to the machine's mainframe. Once Alice goes live and opens the ATM's operating panel, money mules can select any one of the available cassettes and steal money from them at their leisure.
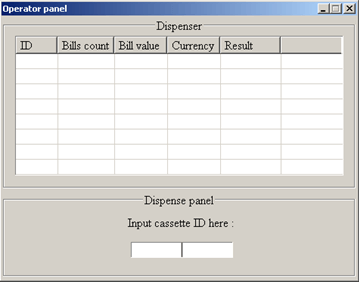
Source: Trend Micro Sancho and Huq correctly note that ATM malware attacks are on the rise:
"Up until recently, ATM malware was a niche category in the malware universe, used by a handful of criminal gangs in a highly targeted manner. We are now at a point where ATM malware is becoming mainstream. The different ATM malware families have been thoroughly analyzed and discussed by many security vendors and these criminals have now started to see the need to hide their creations from the security industry to avoid discovery and detection. Today, they are using commercial off-the-shelf packers; tomorrow we expect to see them start to use custom packers and other obfuscation techniques."
Hopefully, this trend will propel ATM manufacturers to outfit their machines with additional security features. At the same time, financial organizations that purchase these units can help deter bad actors from committing physical ATM attacks by situating their machines inside and/or in full view of a security camera.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

