
A new variant of Android banking malware known as LokiBot triggers ransomware capabilities if a victim attempts to remove it from their infected device. The malware, which bears the same name as a Windows info-stealer that can exfiltrate credentials from over 100 software tools, is making its rounds as a kit sold on hacking forums. Interested parties can purchase a full license with updates for $2,000 in Bitcoin. LokiBot comes with a host of features enabling attackers to prey on suspecting users with Android 4.4 or higher.
They can use the malware to read and send a victim's SMS messages, a capability which they can abuse to send out spam email and try to infect additional users. If successful, they can upload the victims' browser histories to the command and control (C&C) server or conduct an overlay attack on targeted banking apps.
The baddie also comes with several unique features. First, it's capable of starting a user's web browser and opening a web page. Second, it can display notifications under the guise of legitimate applications with the intent of conducting an overlay attack. Perhaps the most intriguing element of LokiBot is its ransomware capabilities. SfyLabs researchers Wesley Gahr, Pham Duy Phuc, and Niels Croese elaborate on this functionality:
"This ransomware triggers when you try to remove LokiBot from the infected device by revoking its administrative rights. It won’t go down without a fight and will encrypt all your files in the external storage as a last resort to steal money from you, as you need to pay Bitcoins to decrypt your files."
The ransomware tells a victim that law enforcement has locked their device "for viewing child pornography." It then asks them to pay between $70 and $100 to regain access of their phone. Fortunately, the user can disable the locker by booting into Safe mode and removing the LokiBot admin and app.
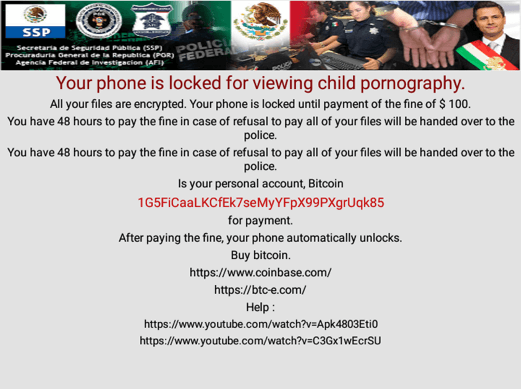
Screen shown when the ransomware locks the phone. (Source: SfyLabs) The malware's ransom-based last resort is supposed to encrypt victims' files with AES. It fails in that regard, however, because it automatically decrypts the encrypted file after deleting the original file and writes back to itself. In so doing, it simply renames the affected files; victims don't lose any of their data.
Of course, other mobile ransomware and hybrid malware won't make the same mistake. Users can protect themselves against such threats by exercising caution around suspicious links and email attachments. They should also be careful to download apps from only trusted developers on Google's Play Store and to read the requested permissions carefully. If a request seems inconsistent with the app's functionality, users should forego installation.

