
The Magnitude exploit kit (EK) is leveraging a recently patched zero-day vulnerability found in Adobe Flash Player to drop CryptoWall ransomware. Early last week, Adobe released a security update for the critical vulnerability CVE-2015-3113, which affects Windows, Macintosh, and Linux. If unpatched, the flaw allows for an attacker to take control of an affected system. Adobe went on to state in its advisory that it was aware of limited attacks targeting the vulnerability. These exploits include those discussed in a recent FireEye report, which details how APT3 (aka UPS), a Chinese threat actor, has all ready incorporated the 0day vulnerability into a large scale phishing campaign against organizations in the aerospace, telecommunications, transportation, and other industries.
"Upon clicking the URLs provided in the phishing emails, targets were redirected to a compromised server hosting JavaScript profiling scripts," explain Erica Eng and Daniel Caselden of FireEye. "Once a target host was profiled, victims downloaded a malicious Adobe Flash Player SWF file and an FLV file, detailed below. This ultimately resulted in a custom backdoor known as SHOTPUT, detected by FireEye as Backdoor.APT.CookieCutter, being delivered to the victim’s system."
Since then, however, security researcher Kafeine discovered that the Magnitude EK has begun exploiting CVE-2015-3113 to drop CryptoWall ransomware in some instances. According to a blog post written by the researcher, malicious SWF and FLV files were used on a machine running on Windows 7 to deliver the ransomware. Kafeine's post was quickly followed by a separate piece of analysis released by Malwarebytes' Jérôme Segura. In his post, the researcher observed the exploit kit to be using the same types of files as those spotted by Kafeine in order to target the Adobe 0day.
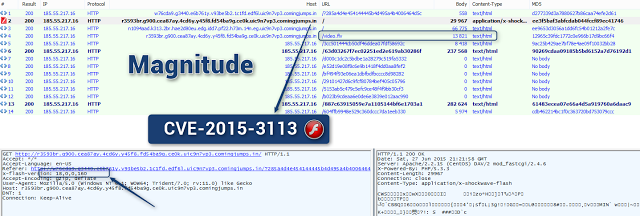
Source: Malware don't need Coffee It is currently unclear how computer criminals have managed to develop exploits for CVE-2015-3113 so quickly. However, it may be the case that the groundwork for these attacks was laid with CVE-2015-3043, another heap overflow security flaw patched by Adobe earlier this year. Peter Pi, a Threat Analyst with TrendLabs, explains the links between those two vulnerabilities here. Given the swiftness with which these exploits were developed, it is important that sysadmins and security professionals work to patch vulnerable machines as soon as a security update becomes available. For more information on how CVE-2015-3113 can be patched, please click here. To learn how you can protect yourself from ransomware, please click here.

