
A malicious image file is distributing the Nemucod malware downloader to unsuspecting users via Facebook chat. Threat intelligence analyst Bart Blaze heard about the malware campaign from a friend. They told him they had received a message on Facebook chat that contained only a Scalable Vector Graphics (SVG) file, which is an XML-based vector image format.
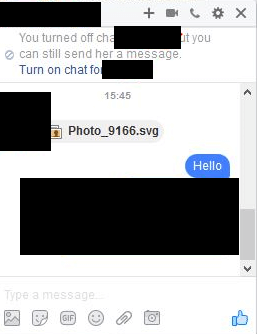
Source: Blaze's Security Blog SVG files allow users to embed content like JavaScript into them, which means an attacker can use them to create a fake image containing malicious code that will execute in most web browsers. Well, that's exactly what the attacker sent to Blaze's friend. Upon taking a closer look at the file, the threat intelligence analyst found lots of obfuscated script that, after opening, redirects a user to a fake YouTube page.
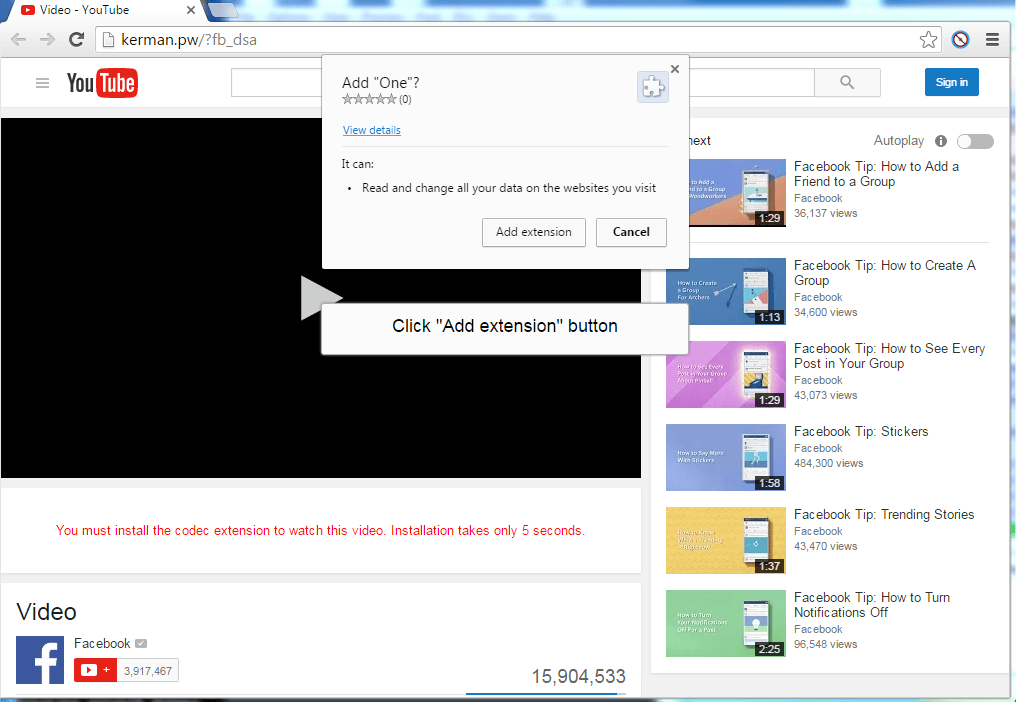
Source: Blaze's Security Blog As you can see in the screenshot's address bar, the web page isn't YouTube at all. It's "kerman.pw," which ends with the country code top-level domain for the Pacific island nation of Palau. Not surprisingly, the page asks the visitor to download a codec that in its permissions says it will be able to read and change all a user's data on every site they visit.
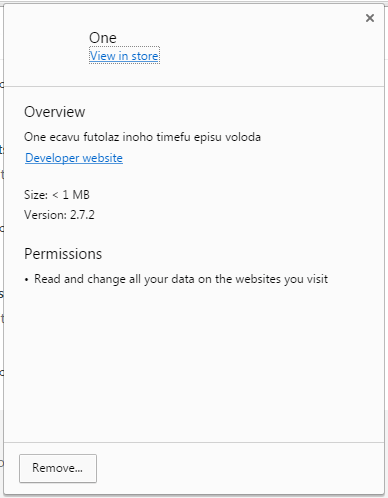
Source: Blaze's Security Blog Blaze hasn't downloaded the codec in a sandbox environment to see what happens, but as he notes in a blog post, no good can come from a file like that:
"Currently, I'm not exactly sure what this extension is supposed to do beside spreading itself automatically via Facebook, but likely it downloads other malware to your machine."
True that! Just look at what security researcher Peter Kruse discovered with one variant of the malware campaign: https://twitter.com/peterkruse/status/800414481545187328 Nemucod is one of those notorious trojans that's never satisfied with just infecting a user's machine. It has a reputation for loading up various other baddies such as Kovter, programs which further jeopardize user's information In this campaign, Nemucod is dropping Locky, a dynamic ransomware strain which has been spotted targeting victims along with the Bizarro Sundown exploit kit. Users can protect themselves against this malware campaign by never clicking on suspicious links, attachments, or image files. They should also maintain an up-to-date anti-virus solution on their computers.

