
A malvertising campaign is distributing code that mines different cryptocurrencies inside an unsuspecting user's web browser. For the operation, computer criminals are targeting mainly visitors to video streaming and in-browser gaming sites based in Russia and Ukraine. They abuse an online advertising network to display ads containing custom JavaScript code. That code is actually an altered version of MineCrunch, a program which mines for cryptocurrency by executing JavaScript inside of a user's browser window. The script performs its code execution covertly and thereby drains the unsuspecting user's computer while it mines for Monero, Feathercoin, and Litecoin. In going after video streaming and gaming sites, attackers have deliberately chosen a target profile that maximizes the productivity of their cryptocurrency mining operations. Bleeping Computer's Catalin Cimpanu elaborates on this point:
"Both types of sites use lots of resources, and users wouldn't get suspicious when their computer slowed down while accessing the site. Furthermore, users tend to linger more on browser games and video streaming services, allowing the mining script to do its job and generate profits for the crooks."
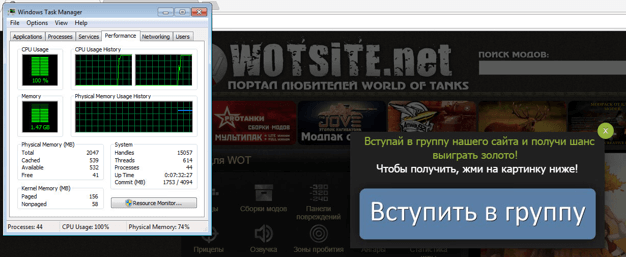
Mining operations taking place while visiting wotsite[.]net. (Source: Bleeping Computer) Bad actors are increasingly resorting to threats equipped with cryptocurrency miners in order to profit off unsuspecting users. In the first eight months of 2017, the number of users unwittingly victimized by cryptocurrency mining software grew to 1.65 million. Threat actors used a number of attack vectors to distribute the software, including free adware installers and technical vulnerabilities like EternalBlue. Given the rise of threats sporting cryptocurrency miners, it's important that users protect themselves against unwanted software installations. First, they should consider activating an ad-blocker inside of their web browsers, as doing so will help block malvertising campaigns. Second, they should consider installing a plugin like NoScript that blocks JavaScript code from automatically executing inside of a web browser by default. Third, they should visit only reputable video streaming and gaming sites that wouldn't, for instance, directly host mining code themselves.

