
Security researchers found that hackers are using both Google Play and Facebook to actively target North Korean defectors with malware capable of stealing their information. McAfee Mobile Research Team discovered that the Sun Team hacking group is using Facebook to share links with North Korean defectors. At the time of analysis, these URLs directed targets to apps on Google Play labeled as "unreleased" versions. One of the apps (Food Ingredients Info) provided users information about food, while the other two (Fast AppLock and AppLockFree) claimed to help secure users' Android devices.
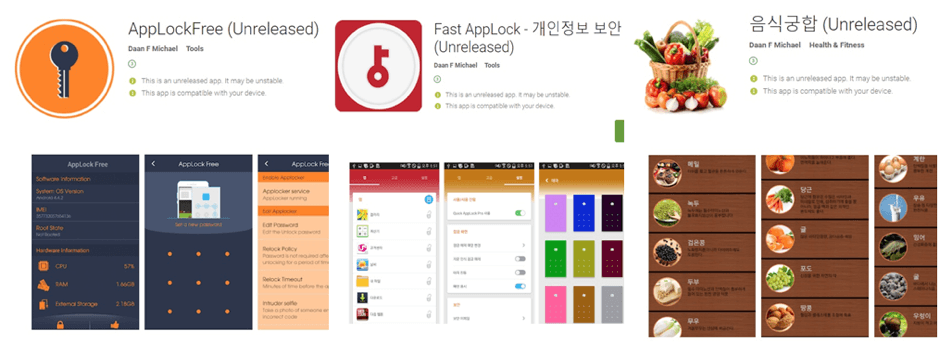
The three apps uploaded on Google Play, which have since been deleted. (Source: McAfee) Upon installation, the apps secretly stole information from the infected device including photos, contact information and SMS messages. The malware then used Dropbox and Yandex to upload the stolen the data and issue commands like plug-in dex files. That's not even the worst part about this campaign. McAfee security researcher Jaewon Min explained as much in a blog post:
The most concerning thing about this Sun Team operation is that they use photos uploaded on social network services and identities of South Koreans to create fake accounts. We have found evidence that some people have had their identities stolen; more could follow. They are using texting and calling services to generate virtual phone numbers so they can sign up for South Korean online services.
Min noted that this is the second campaign detected by McAfee in 2018 through which the Sun Team hacking group targeted North Korean defectors. Given Sun Team's ongoing activity on Google Play Store, not to mention the prevalence of other Android-based malware attacks, McAfee recommended that mobile users take steps to protect themselves by exercising caution around so-called "unreleased" versions of an app. It further advised users to check the downloads and reviews of an app before proceeding with installation.

