
A memory-based malware is using PowerShell scripts within the Windows registry and penetration testing tools to evade detection. Security researchers at Kaspersky Lab came across the malware when they discovered code for Meterpreter, a post-exploitation tool of the Metasploit penetration testing software, inside the physical memory of a domain controller. Analysis of the malware, detected as MEM:Trojan.Win32.Cometer and MEM:Trojan.Win32.Metasploit, yielded PowerShell scripts used from within the Windows registry. Kaspersky's researchers also found the attackers had used the NETSH network configuration scripting utility to tunnel traffic from the host to their command and control (C&C) server. The scripts used by the attackers allocate memory and install Meterpreter to RAM. Using the SC utility, the attackers installed a malicious service to execute one of those scripts on the target computer. They then set up a tunneling service using NETSH to forward all network traffic to their C&C server, allowing them to steal passwords and sensitive information. NETSH, SC, and PowerShell scripts all require privilege escalation. But that's no hurdle for attackers who are familiar with Mimikatz, another Metasploit post-exploitation tool. They simply created a payload that allowed them to steal system administrators' credentials.
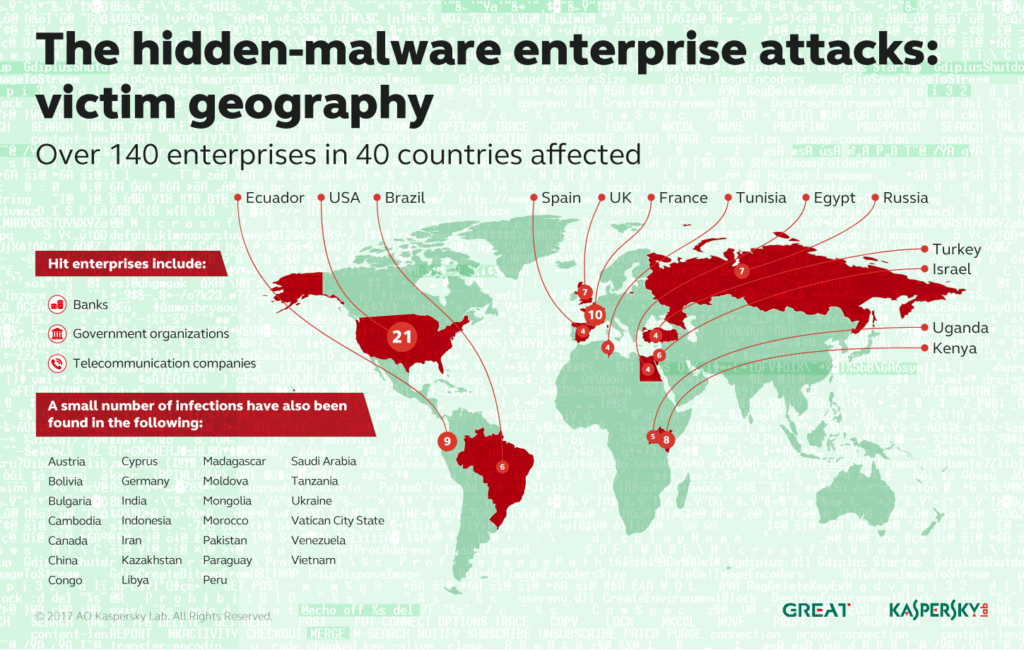
As of this writing, the malware has affected 140 organizations located in 40 countries. It's not clear if the same attacker targeted all those enterprises. That's because attribution in this case is particularly difficult. Kaspersky's researchers elaborate on that point in a blog post:
"During our analysis of the affected bank we learned that the attackers had used several third level domains and domains in the .GA, .ML, .CF ccTLDs. The trick of using such domains is that they are free and missing WHOIS information after domain expiration. Given that the attackers used the Metasploit framework, standard Windows utilities and unknown domains with no WHOIS information, this makes attribution almost impossible."
Nevertheless, some evidence suggests GCMAN and Carbanak could be the responsible parties. This attack is detectable in RAM, network, and registry only. With that in mind, organizations should use Kaspersky's indicators of compromise (IoCs) to protect against this malware. Should they come across it, they should remove the malware from their systems and then change all administrator passwords.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

