
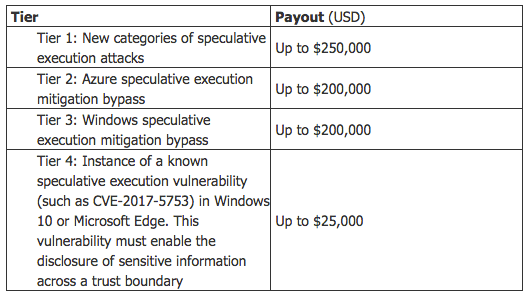
Microsoft has launched a limited-time bug bounty program to help discover and address vulnerabilities similar to Spectre and Meltdown. On 14 March, the Redmond-based tech giant announced a framework for speculative execution side channel vulnerabilities. The program encourages researchers to submit their discoveries of hardware design weaknesses on par with Spectre and Meltown, two vulnerabilities which are responsible for Microsoft's greater focus on preventing CPU side channel attacks. To be eligible for a reward, security researchers must submit a vulnerability report that details a new category or exploitation method for speculative execution side channel vulnerabilities. Responsibly disclosing these types of issues can earn researchers as much as $250,000. Researchers can also report bypasses for mitigations imposed by a hypervisor, Windows, or Microsoft Edge, explain the bug bounty program's guidelines. In so doing, they can expect to receive a bounty of up to $200,000 for Azure or Windows bypasses. Lastly, Microsoft will reward researchers up to $25,000 for vulnerability reports on speculative execution bugs like CVE-2017-5753, Spectre's first variant, that allow attackers to disclose sensitive information across a trust boundary in Windows 10 or Microsoft Edge.
Phillip Misner, principal security group manager at the Microsoft Security Response Center, feels the new bug bounty program is necessary to help the industry address the growing challenge of mitigating hardware vulnerabilities through changes in firmware and software. As quoted in a TechNet blog post:
Speculative execution side channel vulnerabilities require an industry response. To that end, Microsoft will share, under the principles of coordinated vulnerability disclosure, the research disclosed to us under this program so that affected parties can collaborate on solutions to these vulnerabilities. Together with security researchers, we can build a more secure environment for customers.
Microsoft's framework for speculative execution side channel vulnerabilities will be open until 18 December 2018. For terms and conditions of the program, click here. You can also click here to learn more about what Microsoft is doing to address this new class of weaknesses in general.

