
A new report reveals that current blacklists are failing to identify approximately 90% of suspicious IP addresses. The report, "Two Shady Men Walk Into a Bar: Detecting Suspected Malicious Infrastructure Using Hidden Link Analysis," is the culmination of an effort led by threat intelligence firm Recorded Future to illustrate how mentions of malicious IP addresses on the open and dark web, not to mention hidden link analysis of malware, can be used to detect suspicious IP addresses. Between January 1, 2014 and August 2 of this year, Recorded Future examined some 890,000 documents from some 700,000 web sources available online. These sources included websites, news articles, tweets, security blogs, forums, and paste sites. A total of 1,408 different malware were identified as a result of this exercise. After accounting for adware and other qualifications, Recorded Future arrived at 322 unique malware samples.
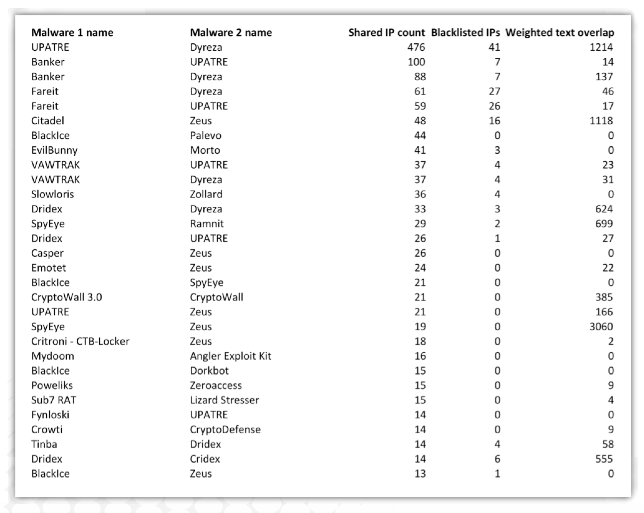
Source: Recorded Future Next, Recorded Future imposed further limitations for the purposes of its study, such as by selecting IP addresses that are only associated with two different malware samples and by removing a number of "whitelisted" IP addresses, such as Google's DNS servers. This resulted in 1,521 IP addresses for 198 different malware.
"We then compared the 1,521 IP addresses against the 258,288 IP addresses currently occurring on the blacklists, and found that only 117 of them were on those list, whereas the rest were unknown and not included on the blacklists," explains Recorded Future in its report. "In other words, 92% of the suspicious IP addresses identified with this method were not identified by current blacklists. Of the 117 addresses, 67 were classified as inbound and 50 as outbound, and 12 of the 117 addresses occurred on multiple blacklists."
The report identifies clusters of IP addresses with which Wiper, Dyre, and other malware are associated. Significantly, Recorded Future's methodology can take this analysis one step further by exploring who plans to exploit the suspicious IP addresses and what tools those actors intend to use. Such a capability could benefit the field of threat intelligence more generally.
"By incorporating this information into the Recorded Future index we can provide it to threat intelligence analysts and also feed it into SIEM systems for improved risk scoring of IP addresses," the report concludes. "This novel approach enables threats to be detected faster and more accurately."
To read the entirety of Recorded Future's analysis, please click here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

