
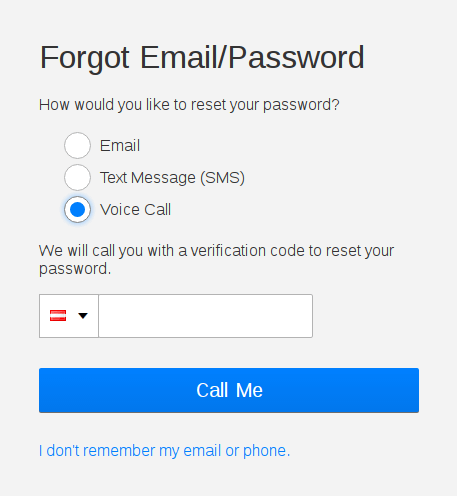
An Austrian security researcher recently unveiled a vulnerability affecting Netflix that allowed attackers to takeover user accounts. In a blog post published on Monday, the researcher – known as ‘Slashcrypto’ – explained the attack works when a victim’s voicemail can be hacked to bypass the password reset function of Netflix. “… When a user wanted to request the code, the user had the possibility to get an automated voice call, which then told the code to the user,” said the researcher.
However, the researcher notes that certain mobile carriers, such as Austria’s T-Mobile network, do not password-protect users’ voicemail by default. This leaves many users vulnerable to the issue of voicemail hacking. An attacker must also be able to spoof the number from which the call is supposedly coming from, although a “very easy” step nowadays due to VoIP, said the researcher. Consequently, the post claims it was possible to take over a target’s Netflix account using the following exploit flow:
- On the Netflix password reset screen, enter the victim’s account ID and corresponding phone number.
- Request a voice call to reset the account password – at the same time, call the victim, so that the automated call gets redirected to the voicemail of the victim.
- Spoof the caller ID to get access to the victim’s mailbox and play the voicemail with the security code.
“This means, that if the victim added a phone number to his/her Netflix account to improve the security of the account, it actually weakened it,” said the researcher.
The bug was reported to Netflix via its responsible disclosure program. “I noticed that they have a really good and fast responding security team,” the researcher added. “It took a little bit longer to fix the issue because the automated phone calls used by Netflix are handled by a third party.” Netflix fixed the bug on November 4 by requiring a key press before the security code gets transmitted to ensure the automated call does not go to voicemail. “This is nothing new, it is no new discovery and everybody who is in security should be aware of this,” concluded the researcher.
“I think, many people do not know that caller ID spoofing, SMS spoofing or E-Mail spoofing even exists and that it is relatively easy to do for everyone,” the researcher warned.
The researcher urges users to set a voicemail password, if their provider offers the feature.

