
Researchers have found a new Android spyware program that's using command and control (C&C) servers previously ran by Hacking Team. Team Red Naga came into contact with the spyware after someone contacted them about "advanced malware" that had infected one of their co-workers. Early on in their analysis, Team Red Naga didn't find anything particularly interesting about program. It claimed to be a legitimate update for Android, and it also requested almost every permission.
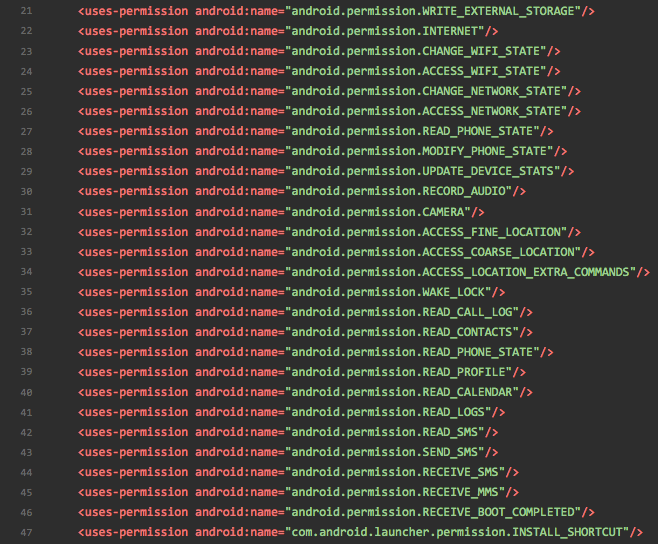
Source: Team Red Naga Yeah, yeah...we've seen it before. The research team grew hopeful when they found some encrypted/obfuscated strings after they threw the Dex file into IDA Pro. But after decrypting the strings, they didn't find anything groundbreaking. Only class names and method names typical of any spyware, including the ability to record audio/video and to create screen shots. It wasn't until the researchers looked into the malware's data exfiltration scheme, particularly its two C&C servers, that they found something. As they explain in a blog post:
"These are interesting as they are not using domains which could mean a few things. One is that these people are lazy. Another possibility is that they’re purposefully avoiding DNS to avoid getting detected by anyone smart enough to use passive DNS searching. Everyone in the information security space knows DNS is the (old) new hotness and maybe they realize this. Without telling a friend what exactly I was investigating, I shared these IP addresses. They plugged them into whatever information feeds they had and something popped up. Oh hey, these appear to be previously used HackingTeam C2s! (the author's emphasis)"
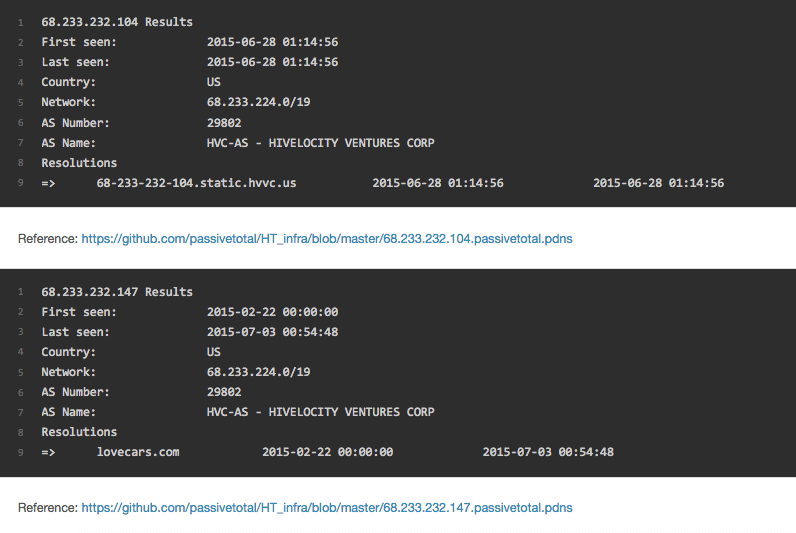
Source: Team Red Naga Interesting! It begs the question: did the Italian spyware firm that suffered a breach in 2015 produce the Android malware, or was the spyware using those C&C servers just out of coincidence? That's hard to say. Two former Hacking Team employees told Motherboard they were certain their former employer did not produce the malware, as did an anonymous security researcher:
"The sample has nothing to do with Hacking Team. It’s structurally different from the ones attributed to Hacking Team and doesn’t share any part of the code.”
Instead, researchers suspect the spyware might belong to Raxir, a surveillance firm which is also based in Italy. That's because of a string they found the program's code:
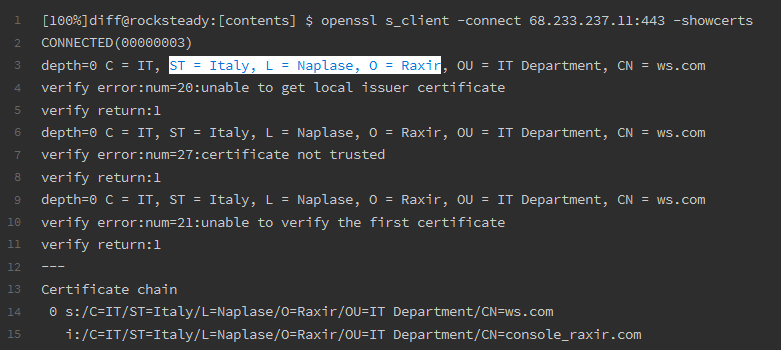
Source: Bleeping Computer Regardless of the identity of its developers, one thing's for certain: users need to protect themselves against the spyware and programs like it. They can do so by maintaining an up-to-date anti-virus solution on their phones, by avoiding clicking on suspicious links and email attachments, and by updating their devices (if and when that's possible).

