
A new variant of the SamSam ransomware family requires direct involvement from attackers in order to execute its malware payload. Uncovered by Malwarebytes, new versions of SamSam require attackers to execute a batch file that's responsible for loading up a .NET runner. They do so by manually entering a password as the file's command-line parameter and without the use of a separate file. The password is then passed down the infection chain to the .NET runner, which uses it for decryption of an encrypted stub file in order to execute the main malware payload.
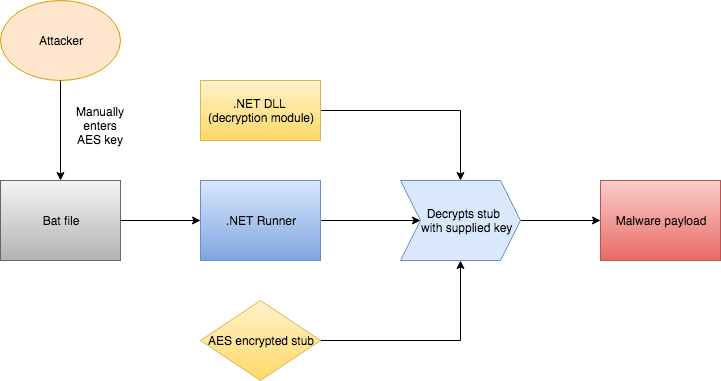
A flow chart detailing the SamSam variant's execution method. (Source: Malwarebytes) This password makes it difficult for researchers to analyze the latest versions of SamSam's malware payload. They need the password to do so, but they can't obtain it unless they essentially intercept it at the time of an attack. Without the password, there's only so much they can learn about SamSam's evolution, including whether there are any errors they can exploit to develop a decryptor sometime in the future. Allan Liska, Senior Solutions Architect at Recorded Future, told Bleeping Computer that the addition of the password points to the sophistication of SamSam's operators:
That password appears to be set at compile time, which means each campaign may have a different password associated with it. While, to the best of our knowledge, the SamSam group is not a nation state actor, these tactics, protecting the code from security researchers and limiting the exposure of your tools, are very similar to what nation state actors do.
So far, those malefactors have leveraged their close control of SamSam to infect large organizations like hospitals and government entities. Given those attacks, healthcare providers need to make sure they take steps to lock down their environments. Here is some guidance on how to do so.

